|
|
||
|---|---|---|
| clusters | ||
| doc/images | ||
| galaxies | ||
| misp | ||
| vocabularies | ||
| .travis.yml | ||
| README.md | ||
README.md
misp-galaxy
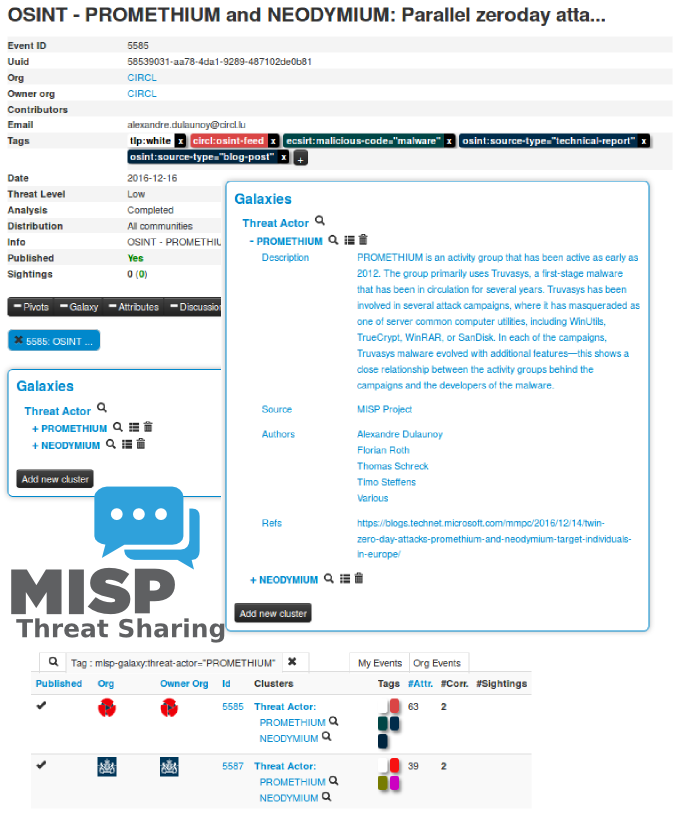
MISP galaxy is a simple method to express a large object called cluster that can be attached to MISP events or attributes. A cluster can be composed of one or more elements. Elements are expressed as key-values. There are default vocabularies available in MISP galaxy but those can be overwritten, replaced or updated as you wish.
Existing clusters and vocabularies can be used as-is or as a template. MISP distribution can be applied to each cluster to permit a limited or broader distribution scheme.
Vocabularies are from existing standards (like STIX, Veris, MISP and so on) or custom ones.
The objective is to have a comment set of clusters for organizations starting analysis but that can be expanded to localized information (which is not shared) or additional information (that can be shared).
Available clusters
- clusters/microsoft-activity-group.json - Activity groups as described by Microsoft
- clusters/threat-actor.json - Adversary groups - Known or estimated adversary groups targeting organizations and employees. Adversary groups are regularly confused with their initial operation or campaign. MISP
- clusters/tool.json - tool is an enumeration of tools used by adversaries. The list includes malware but also common software regularly used by the adversaries. MISP
Available Vocabularies
Common
- vocabularies/common/certainty-level.json - Certainty level of an associated element or cluster.
Threat Actor
- vocabularies/threat-actor/intended-effect-vocabulary.json - The IntendedEffectVocab is the default STIX vocabulary for expressing the intended effect of a threat actor. STIX 1.2.1
- vocabularies/threat-actor/motivation-vocabulary.json - The MotivationVocab is the default STIX vocabulary for expressing the motivation of a threat actor. STIX 1.2.1
- vocabularies/threat-actor/planning-and-operational-support-vocabulary.json - The PlanningAndOperationalSupportVocab is the default STIX vocabulary for expressing the planning and operational support functions available to a threat actor.
- vocabularies/threat-actor/sophistication.json - The ThreatActorSophisticationVocab enumeration is used to define the default STIX vocabulary for expressing the subjective level of sophistication of a threat actor.
- vocabularies/threat-actor/type.json - The ThreatActorTypeVocab enumeration is used to define the default STIX vocabulary for expressing the subjective type of a threat actor.
MISP Integration
Starting from MISP 2.4.56, galaxy is integrated within the MISP threat sharing platform and users can directly benefit from the available clusters to attach them to the MISP event.
How to contribute?
In the world of threat intelligence, there are many different models or approaches to order, classify or describe threat actors, threats or activity groups. We welcome new ways of describing threat intelligence as the galaxy model allows to reuse the ones you use or trust for your organization or community.
Fork the project, update or create elements or clusters and make a pull-request.
We recommend to validate the JSON file using jq before doing a pull-request.
License
MISP galaxy is licensed under CC0 1.0 Universal (CC0 1.0) - Public Domain Dedication.