2022-04-26 11:27:11 +02:00
|
|
|
# Copyright 2014-2022 The Matrix.org Foundation C.I.C.
|
2021-06-09 20:39:51 +02:00
|
|
|
# Copyright 2020 Sorunome
|
2014-08-12 16:10:52 +02:00
|
|
|
#
|
|
|
|
|
# Licensed under the Apache License, Version 2.0 (the "License");
|
|
|
|
|
# you may not use this file except in compliance with the License.
|
|
|
|
|
# You may obtain a copy of the License at
|
|
|
|
|
#
|
|
|
|
|
# http://www.apache.org/licenses/LICENSE-2.0
|
|
|
|
|
#
|
|
|
|
|
# Unless required by applicable law or agreed to in writing, software
|
|
|
|
|
# distributed under the License is distributed on an "AS IS" BASIS,
|
|
|
|
|
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
|
|
|
|
# See the License for the specific language governing permissions and
|
|
|
|
|
# limitations under the License.
|
2014-08-13 04:14:34 +02:00
|
|
|
|
2014-08-12 16:10:52 +02:00
|
|
|
"""Contains handlers for federation events."""
|
2018-04-17 23:11:19 +02:00
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
import enum
|
|
|
|
|
import itertools
|
2018-04-17 23:11:19 +02:00
|
|
|
import logging
|
2022-04-26 11:27:11 +02:00
|
|
|
from enum import Enum
|
2020-06-16 14:51:47 +02:00
|
|
|
from http import HTTPStatus
|
2021-08-26 22:41:44 +02:00
|
|
|
from typing import TYPE_CHECKING, Dict, Iterable, List, Optional, Tuple, Union
|
2018-04-17 23:11:19 +02:00
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
import attr
|
2018-07-09 08:09:20 +02:00
|
|
|
from signedjson.key import decode_verify_key_bytes
|
|
|
|
|
from signedjson.sign import verify_signed_json
|
2016-02-23 16:11:25 +01:00
|
|
|
from unpaddedbase64 import decode_base64
|
2014-08-12 16:10:52 +02:00
|
|
|
|
2019-10-18 19:43:36 +02:00
|
|
|
from synapse import event_auth
|
2021-10-19 11:24:09 +02:00
|
|
|
from synapse.api.constants import EventContentFields, EventTypes, Membership
|
2014-11-26 17:06:20 +01:00
|
|
|
from synapse.api.errors import (
|
2018-07-09 08:09:20 +02:00
|
|
|
AuthError,
|
|
|
|
|
CodeMessageException,
|
2019-06-12 11:31:37 +02:00
|
|
|
Codes,
|
2018-01-22 19:11:18 +01:00
|
|
|
FederationDeniedError,
|
2020-05-22 12:39:20 +02:00
|
|
|
HttpResponseException,
|
2020-07-16 16:17:31 +02:00
|
|
|
NotFoundError,
|
2019-06-03 10:56:45 +02:00
|
|
|
RequestSendFailed,
|
2018-07-09 08:09:20 +02:00
|
|
|
SynapseError,
|
2014-11-26 17:06:20 +01:00
|
|
|
)
|
2021-10-19 11:24:09 +02:00
|
|
|
from synapse.api.room_versions import KNOWN_ROOM_VERSIONS, RoomVersion
|
2019-01-23 21:05:44 +01:00
|
|
|
from synapse.crypto.event_signing import compute_event_signature
|
2021-10-19 11:24:09 +02:00
|
|
|
from synapse.event_auth import validate_event_for_room_version
|
2020-01-28 15:18:29 +01:00
|
|
|
from synapse.events import EventBase
|
2019-11-01 17:19:09 +01:00
|
|
|
from synapse.events.snapshot import EventContext
|
2018-07-09 08:09:20 +02:00
|
|
|
from synapse.events.validator import EventValidator
|
2021-08-26 19:34:57 +02:00
|
|
|
from synapse.federation.federation_client import InvalidResponseError
|
2020-11-19 11:05:33 +01:00
|
|
|
from synapse.http.servlet import assert_params_in_dict
|
2022-03-09 12:00:48 +01:00
|
|
|
from synapse.logging.context import nested_logging_context
|
2022-02-22 14:33:22 +01:00
|
|
|
from synapse.metrics.background_process_metrics import run_as_background_process
|
2018-07-26 12:44:22 +02:00
|
|
|
from synapse.replication.http.federation import (
|
2018-08-09 11:29:48 +02:00
|
|
|
ReplicationCleanRoomRestServlet,
|
2020-11-13 17:24:04 +01:00
|
|
|
ReplicationStoreRoomOnOutlierMembershipRestServlet,
|
2018-07-26 12:44:22 +02:00
|
|
|
)
|
2020-08-05 22:38:57 +02:00
|
|
|
from synapse.storage.databases.main.events_worker import EventRedactBehaviour
|
2021-08-26 22:41:44 +02:00
|
|
|
from synapse.types import JsonDict, StateMap, get_domain_from_id
|
|
|
|
|
from synapse.util.async_helpers import Linearizer
|
2015-05-12 11:35:45 +02:00
|
|
|
from synapse.util.retryutils import NotRetryingDestination
|
2018-07-16 12:38:45 +02:00
|
|
|
from synapse.visibility import filter_events_for_server
|
2015-05-12 11:35:45 +02:00
|
|
|
|
2020-09-28 16:20:02 +02:00
|
|
|
if TYPE_CHECKING:
|
|
|
|
|
from synapse.server import HomeServer
|
|
|
|
|
|
2014-08-12 16:10:52 +02:00
|
|
|
logger = logging.getLogger(__name__)
|
|
|
|
|
|
2019-12-05 16:02:35 +01:00
|
|
|
|
2021-12-02 08:02:20 +01:00
|
|
|
def get_domains_from_state(state: StateMap[EventBase]) -> List[Tuple[str, int]]:
|
|
|
|
|
"""Get joined domains from state
|
|
|
|
|
|
|
|
|
|
Args:
|
|
|
|
|
state: State map from type/state key to event.
|
|
|
|
|
|
|
|
|
|
Returns:
|
|
|
|
|
Returns a list of servers with the lowest depth of their joins.
|
|
|
|
|
Sorted by lowest depth first.
|
|
|
|
|
"""
|
|
|
|
|
joined_users = [
|
|
|
|
|
(state_key, int(event.depth))
|
|
|
|
|
for (e_type, state_key), event in state.items()
|
|
|
|
|
if e_type == EventTypes.Member and event.membership == Membership.JOIN
|
|
|
|
|
]
|
|
|
|
|
|
|
|
|
|
joined_domains: Dict[str, int] = {}
|
|
|
|
|
for u, d in joined_users:
|
|
|
|
|
try:
|
|
|
|
|
dom = get_domain_from_id(u)
|
|
|
|
|
old_d = joined_domains.get(dom)
|
|
|
|
|
if old_d:
|
|
|
|
|
joined_domains[dom] = min(d, old_d)
|
|
|
|
|
else:
|
|
|
|
|
joined_domains[dom] = d
|
|
|
|
|
except Exception:
|
|
|
|
|
pass
|
|
|
|
|
|
|
|
|
|
return sorted(joined_domains.items(), key=lambda d: d[1])
|
|
|
|
|
|
|
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
class _BackfillPointType(Enum):
|
|
|
|
|
# a regular backwards extremity (ie, an event which we don't yet have, but which
|
|
|
|
|
# is referred to by other events in the DAG)
|
|
|
|
|
BACKWARDS_EXTREMITY = enum.auto()
|
|
|
|
|
|
|
|
|
|
# an MSC2716 "insertion event"
|
|
|
|
|
INSERTION_PONT = enum.auto()
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
@attr.s(slots=True, auto_attribs=True, frozen=True)
|
|
|
|
|
class _BackfillPoint:
|
|
|
|
|
"""A potential point we might backfill from"""
|
|
|
|
|
|
|
|
|
|
event_id: str
|
|
|
|
|
depth: int
|
|
|
|
|
type: _BackfillPointType
|
|
|
|
|
|
|
|
|
|
|
2021-10-08 13:44:43 +02:00
|
|
|
class FederationHandler:
|
2021-08-26 22:41:44 +02:00
|
|
|
"""Handles general incoming federation requests
|
|
|
|
|
|
|
|
|
|
Incoming events are *not* handled here, for which see FederationEventHandler.
|
2014-08-26 20:49:42 +02:00
|
|
|
"""
|
2014-08-12 16:10:52 +02:00
|
|
|
|
2020-09-28 16:20:02 +02:00
|
|
|
def __init__(self, hs: "HomeServer"):
|
2015-11-05 17:43:19 +01:00
|
|
|
self.hs = hs
|
|
|
|
|
|
2022-02-23 12:04:02 +01:00
|
|
|
self.store = hs.get_datastores().main
|
2019-10-23 13:02:36 +02:00
|
|
|
self.storage = hs.get_storage()
|
2019-10-23 18:25:54 +02:00
|
|
|
self.state_store = self.storage.state
|
2018-07-31 16:44:05 +02:00
|
|
|
self.federation_client = hs.get_federation_client()
|
2014-08-26 20:49:42 +02:00
|
|
|
self.state_handler = hs.get_state_handler()
|
|
|
|
|
self.server_name = hs.hostname
|
2014-11-14 17:45:39 +01:00
|
|
|
self.keyring = hs.get_keyring()
|
2017-06-30 17:20:30 +02:00
|
|
|
self.is_mine_id = hs.is_mine_id
|
2017-10-03 14:53:09 +02:00
|
|
|
self.spam_checker = hs.get_spam_checker()
|
2018-01-15 17:52:07 +01:00
|
|
|
self.event_creation_handler = hs.get_event_creation_handler()
|
2021-10-08 13:44:43 +02:00
|
|
|
self.event_builder_factory = hs.get_event_builder_factory()
|
2021-04-23 13:05:51 +02:00
|
|
|
self._event_auth_handler = hs.get_event_auth_handler()
|
2021-09-24 13:25:21 +02:00
|
|
|
self._server_notices_mxid = hs.config.servernotices.server_notices_mxid
|
2018-07-25 17:32:05 +02:00
|
|
|
self.config = hs.config
|
2020-12-02 17:09:24 +01:00
|
|
|
self.http_client = hs.get_proxied_blacklisted_http_client()
|
2020-05-22 15:21:54 +02:00
|
|
|
self._replication = hs.get_replication_data_handler()
|
2021-08-26 22:41:44 +02:00
|
|
|
self._federation_event_handler = hs.get_federation_event_handler()
|
2014-08-26 20:49:42 +02:00
|
|
|
|
2019-06-20 11:32:02 +02:00
|
|
|
self._clean_room_for_join_client = ReplicationCleanRoomRestServlet.make_client(
|
|
|
|
|
hs
|
2018-08-09 11:29:48 +02:00
|
|
|
)
|
2014-08-26 20:49:42 +02:00
|
|
|
|
2021-09-13 19:07:12 +02:00
|
|
|
if hs.config.worker.worker_app:
|
2021-02-16 23:32:34 +01:00
|
|
|
self._maybe_store_room_on_outlier_membership = (
|
|
|
|
|
ReplicationStoreRoomOnOutlierMembershipRestServlet.make_client(hs)
|
2020-02-26 17:58:33 +01:00
|
|
|
)
|
2020-01-30 18:06:38 +01:00
|
|
|
else:
|
2020-11-13 17:24:04 +01:00
|
|
|
self._maybe_store_room_on_outlier_membership = (
|
|
|
|
|
self.store.maybe_store_room_on_outlier_membership
|
|
|
|
|
)
|
2020-01-30 18:06:38 +01:00
|
|
|
|
2021-06-04 11:47:58 +02:00
|
|
|
self._room_backfill = Linearizer("room_backfill")
|
|
|
|
|
|
2019-06-12 11:31:37 +02:00
|
|
|
self.third_party_event_rules = hs.get_third_party_event_rules()
|
|
|
|
|
|
2020-09-18 15:25:52 +02:00
|
|
|
async def maybe_backfill(
|
|
|
|
|
self, room_id: str, current_depth: int, limit: int
|
|
|
|
|
) -> bool:
|
2015-05-12 11:35:45 +02:00
|
|
|
"""Checks the database to see if we should backfill before paginating,
|
|
|
|
|
and if so do.
|
2020-09-18 15:25:52 +02:00
|
|
|
|
|
|
|
|
Args:
|
|
|
|
|
room_id
|
|
|
|
|
current_depth: The depth from which we're paginating from. This is
|
|
|
|
|
used to decide if we should backfill and what extremities to
|
|
|
|
|
use.
|
|
|
|
|
limit: The number of events that the pagination request will
|
|
|
|
|
return. This is used as part of the heuristic to decide if we
|
|
|
|
|
should back paginate.
|
2015-05-11 19:01:31 +02:00
|
|
|
"""
|
2022-04-05 16:43:52 +02:00
|
|
|
async with self._room_backfill.queue(room_id):
|
2021-06-04 11:47:58 +02:00
|
|
|
return await self._maybe_backfill_inner(room_id, current_depth, limit)
|
|
|
|
|
|
|
|
|
|
async def _maybe_backfill_inner(
|
|
|
|
|
self, room_id: str, current_depth: int, limit: int
|
|
|
|
|
) -> bool:
|
2022-04-26 11:27:11 +02:00
|
|
|
backwards_extremities = [
|
|
|
|
|
_BackfillPoint(event_id, depth, _BackfillPointType.BACKWARDS_EXTREMITY)
|
|
|
|
|
for event_id, depth in await self.store.get_oldest_event_ids_with_depth_in_room(
|
|
|
|
|
room_id
|
|
|
|
|
)
|
|
|
|
|
]
|

Fix historical messages backfilling in random order on remote homeservers (MSC2716) (#11114)
Fix https://github.com/matrix-org/synapse/issues/11091
Fix https://github.com/matrix-org/synapse/issues/10764 (side-stepping the issue because we no longer have to deal with `fake_prev_event_id`)
1. Made the `/backfill` response return messages in `(depth, stream_ordering)` order (previously only sorted by `depth`)
- Technically, it shouldn't really matter how `/backfill` returns things but I'm just trying to make the `stream_ordering` a little more consistent from the origin to the remote homeservers in order to get the order of messages from `/messages` consistent ([sorted by `(topological_ordering, stream_ordering)`](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)).
- Even now that we return backfilled messages in order, it still doesn't guarantee the same `stream_ordering` (and more importantly the [`/messages` order](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)) on the other server. For example, if a room has a bunch of history imported and someone visits a permalink to a historical message back in time, their homeserver will skip over the historical messages in between and insert the permalink as the next message in the `stream_order` and totally throw off the sort.
- This will be even more the case when we add the [MSC3030 jump to date API endpoint](https://github.com/matrix-org/matrix-doc/pull/3030) so the static archives can navigate and jump to a certain date.
- We're solving this in the future by switching to [online topological ordering](https://github.com/matrix-org/gomatrixserverlib/issues/187) and [chunking](https://github.com/matrix-org/synapse/issues/3785) which by its nature will apply retroactively to fix any inconsistencies introduced by people permalinking
2. As we're navigating `prev_events` to return in `/backfill`, we order by `depth` first (newest -> oldest) and now also tie-break based on the `stream_ordering` (newest -> oldest). This is technically important because MSC2716 inserts a bunch of historical messages at the same `depth` so it's best to be prescriptive about which ones we should process first. In reality, I think the code already looped over the historical messages as expected because the database is already in order.
3. Making the historical state chain and historical event chain float on their own by having no `prev_events` instead of a fake `prev_event` which caused backfill to get clogged with an unresolvable event. Fixes https://github.com/matrix-org/synapse/issues/11091 and https://github.com/matrix-org/synapse/issues/10764
4. We no longer find connected insertion events by finding a potential `prev_event` connection to the current event we're iterating over. We now solely rely on marker events which when processed, add the insertion event as an extremity and the federating homeserver can ask about it when time calls.
- Related discussion, https://github.com/matrix-org/synapse/pull/11114#discussion_r741514793
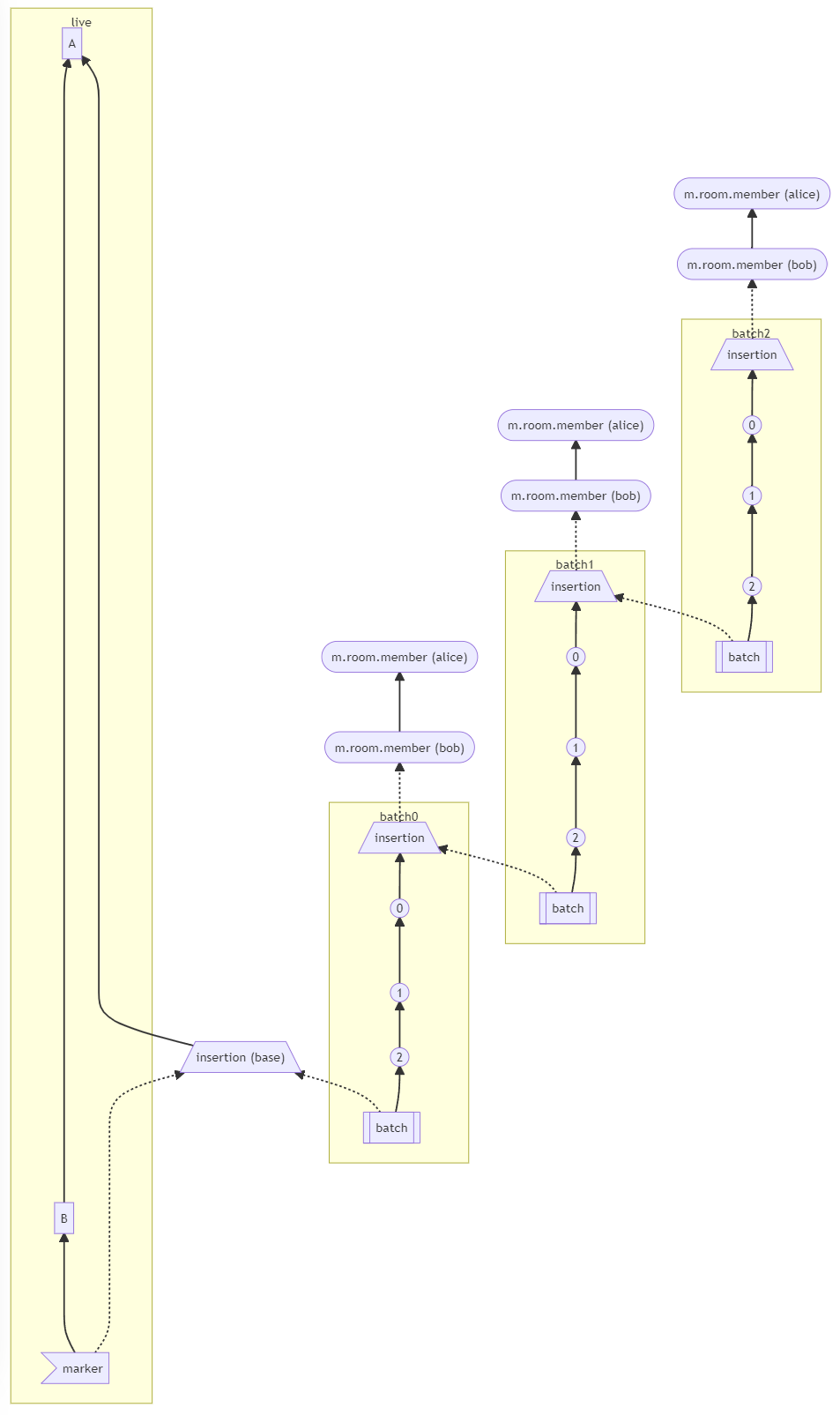
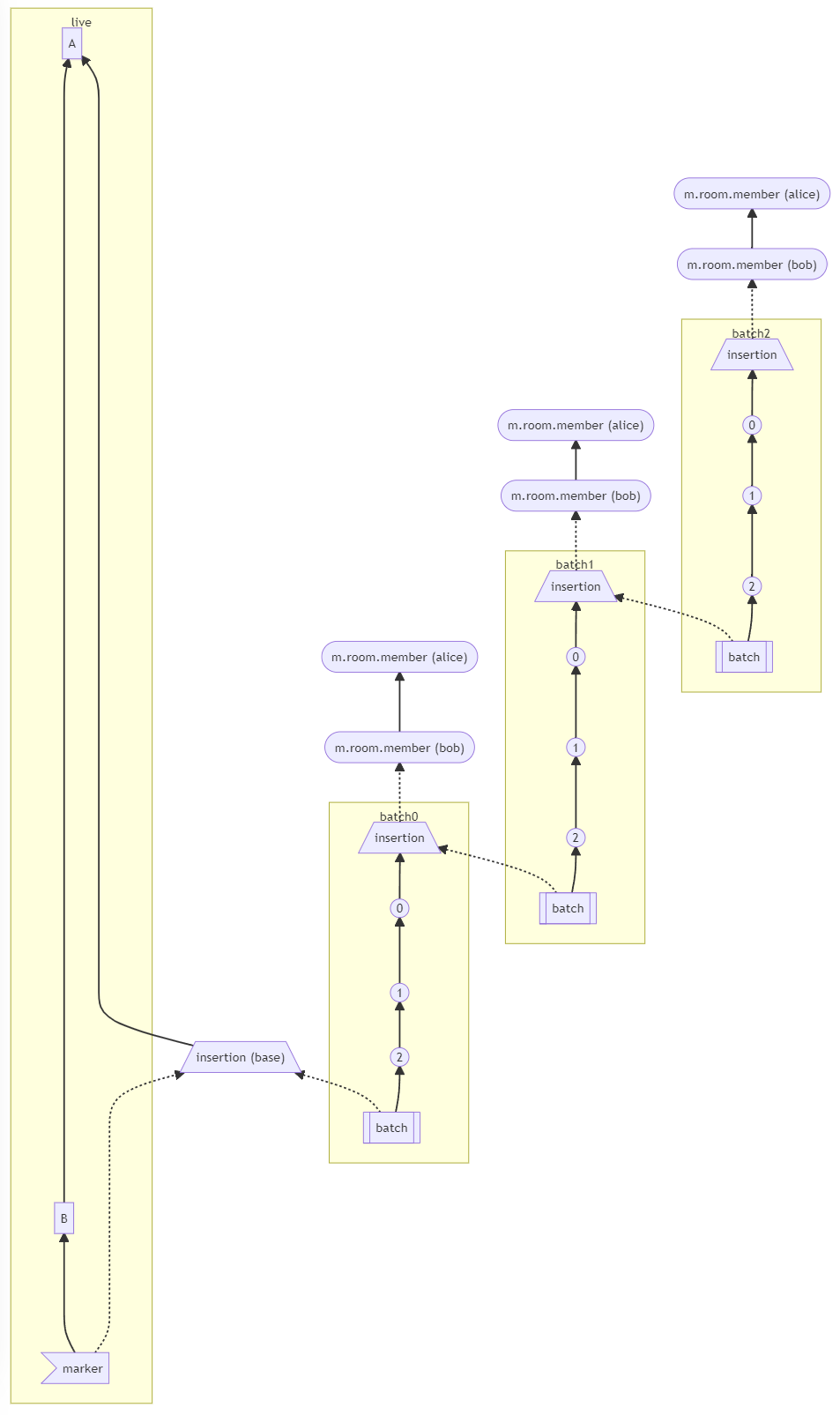
Before | After
--- | ---
 | 
#### Why aren't we sorting topologically when receiving backfill events?
> The main reason we're going to opt to not sort topologically when receiving backfill events is because it's probably best to do whatever is easiest to make it just work. People will probably have opinions once they look at [MSC2716](https://github.com/matrix-org/matrix-doc/pull/2716) which could change whatever implementation anyway.
>
> As mentioned, ideally we would do this but code necessary to make the fake edges but it gets confusing and gives an impression of “just whyyyy” (feels icky). This problem also dissolves with online topological ordering.
>
> -- https://github.com/matrix-org/synapse/pull/11114#discussion_r741517138
See https://github.com/matrix-org/synapse/pull/11114#discussion_r739610091 for the technical difficulties
2022-02-07 22:54:13 +01:00
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
insertion_events_to_be_backfilled: List[_BackfillPoint] = []
|

Fix historical messages backfilling in random order on remote homeservers (MSC2716) (#11114)
Fix https://github.com/matrix-org/synapse/issues/11091
Fix https://github.com/matrix-org/synapse/issues/10764 (side-stepping the issue because we no longer have to deal with `fake_prev_event_id`)
1. Made the `/backfill` response return messages in `(depth, stream_ordering)` order (previously only sorted by `depth`)
- Technically, it shouldn't really matter how `/backfill` returns things but I'm just trying to make the `stream_ordering` a little more consistent from the origin to the remote homeservers in order to get the order of messages from `/messages` consistent ([sorted by `(topological_ordering, stream_ordering)`](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)).
- Even now that we return backfilled messages in order, it still doesn't guarantee the same `stream_ordering` (and more importantly the [`/messages` order](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)) on the other server. For example, if a room has a bunch of history imported and someone visits a permalink to a historical message back in time, their homeserver will skip over the historical messages in between and insert the permalink as the next message in the `stream_order` and totally throw off the sort.
- This will be even more the case when we add the [MSC3030 jump to date API endpoint](https://github.com/matrix-org/matrix-doc/pull/3030) so the static archives can navigate and jump to a certain date.
- We're solving this in the future by switching to [online topological ordering](https://github.com/matrix-org/gomatrixserverlib/issues/187) and [chunking](https://github.com/matrix-org/synapse/issues/3785) which by its nature will apply retroactively to fix any inconsistencies introduced by people permalinking
2. As we're navigating `prev_events` to return in `/backfill`, we order by `depth` first (newest -> oldest) and now also tie-break based on the `stream_ordering` (newest -> oldest). This is technically important because MSC2716 inserts a bunch of historical messages at the same `depth` so it's best to be prescriptive about which ones we should process first. In reality, I think the code already looped over the historical messages as expected because the database is already in order.
3. Making the historical state chain and historical event chain float on their own by having no `prev_events` instead of a fake `prev_event` which caused backfill to get clogged with an unresolvable event. Fixes https://github.com/matrix-org/synapse/issues/11091 and https://github.com/matrix-org/synapse/issues/10764
4. We no longer find connected insertion events by finding a potential `prev_event` connection to the current event we're iterating over. We now solely rely on marker events which when processed, add the insertion event as an extremity and the federating homeserver can ask about it when time calls.
- Related discussion, https://github.com/matrix-org/synapse/pull/11114#discussion_r741514793
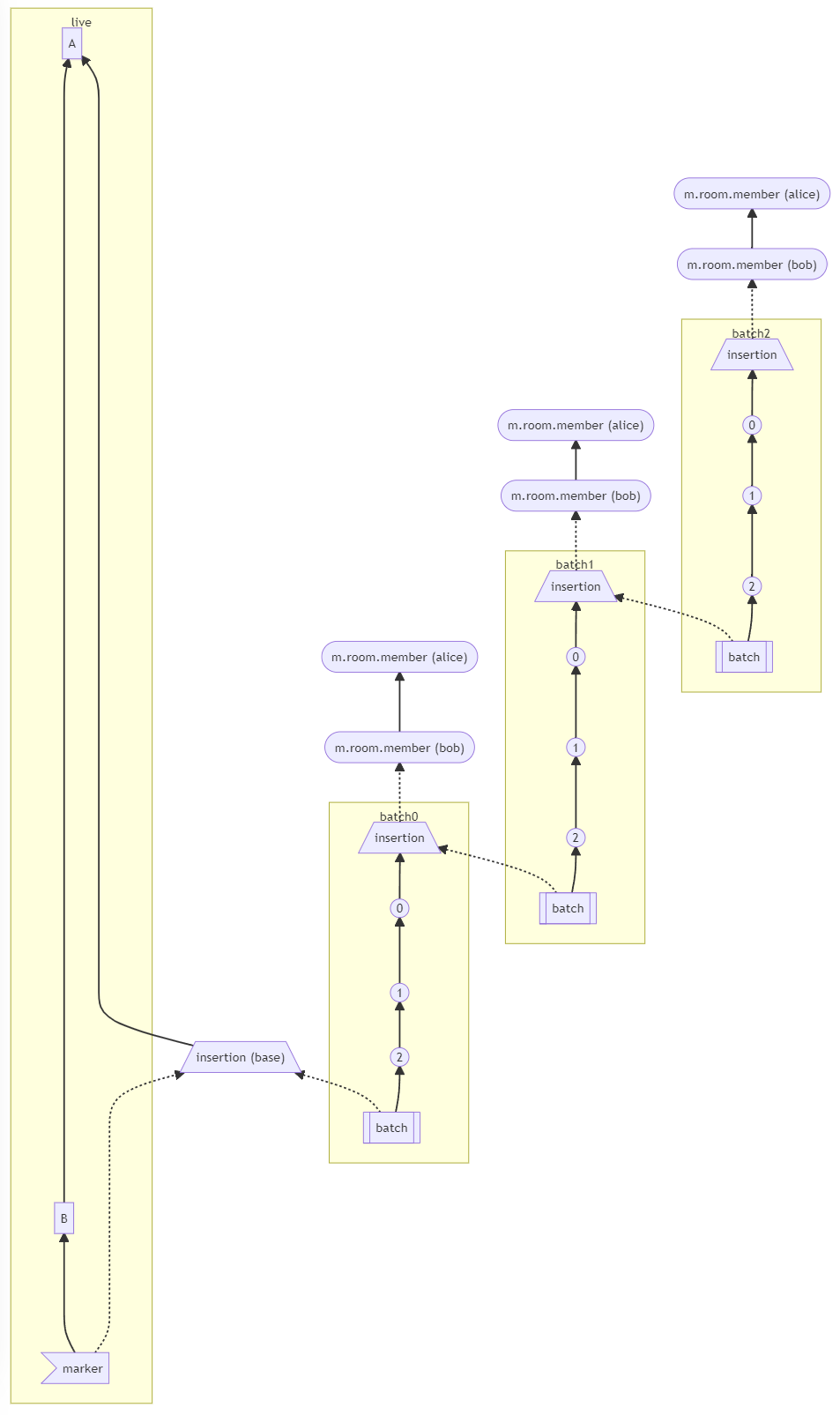
Before | After
--- | ---
 | 
#### Why aren't we sorting topologically when receiving backfill events?
> The main reason we're going to opt to not sort topologically when receiving backfill events is because it's probably best to do whatever is easiest to make it just work. People will probably have opinions once they look at [MSC2716](https://github.com/matrix-org/matrix-doc/pull/2716) which could change whatever implementation anyway.
>
> As mentioned, ideally we would do this but code necessary to make the fake edges but it gets confusing and gives an impression of “just whyyyy” (feels icky). This problem also dissolves with online topological ordering.
>
> -- https://github.com/matrix-org/synapse/pull/11114#discussion_r741517138
See https://github.com/matrix-org/synapse/pull/11114#discussion_r739610091 for the technical difficulties
2022-02-07 22:54:13 +01:00
|
|
|
if self.hs.config.experimental.msc2716_enabled:
|
2022-04-26 11:27:11 +02:00
|
|
|
insertion_events_to_be_backfilled = [
|
|
|
|
|
_BackfillPoint(event_id, depth, _BackfillPointType.INSERTION_PONT)
|
|
|
|
|
for event_id, depth in await self.store.get_insertion_event_backward_extremities_in_room(
|

Fix historical messages backfilling in random order on remote homeservers (MSC2716) (#11114)
Fix https://github.com/matrix-org/synapse/issues/11091
Fix https://github.com/matrix-org/synapse/issues/10764 (side-stepping the issue because we no longer have to deal with `fake_prev_event_id`)
1. Made the `/backfill` response return messages in `(depth, stream_ordering)` order (previously only sorted by `depth`)
- Technically, it shouldn't really matter how `/backfill` returns things but I'm just trying to make the `stream_ordering` a little more consistent from the origin to the remote homeservers in order to get the order of messages from `/messages` consistent ([sorted by `(topological_ordering, stream_ordering)`](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)).
- Even now that we return backfilled messages in order, it still doesn't guarantee the same `stream_ordering` (and more importantly the [`/messages` order](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)) on the other server. For example, if a room has a bunch of history imported and someone visits a permalink to a historical message back in time, their homeserver will skip over the historical messages in between and insert the permalink as the next message in the `stream_order` and totally throw off the sort.
- This will be even more the case when we add the [MSC3030 jump to date API endpoint](https://github.com/matrix-org/matrix-doc/pull/3030) so the static archives can navigate and jump to a certain date.
- We're solving this in the future by switching to [online topological ordering](https://github.com/matrix-org/gomatrixserverlib/issues/187) and [chunking](https://github.com/matrix-org/synapse/issues/3785) which by its nature will apply retroactively to fix any inconsistencies introduced by people permalinking
2. As we're navigating `prev_events` to return in `/backfill`, we order by `depth` first (newest -> oldest) and now also tie-break based on the `stream_ordering` (newest -> oldest). This is technically important because MSC2716 inserts a bunch of historical messages at the same `depth` so it's best to be prescriptive about which ones we should process first. In reality, I think the code already looped over the historical messages as expected because the database is already in order.
3. Making the historical state chain and historical event chain float on their own by having no `prev_events` instead of a fake `prev_event` which caused backfill to get clogged with an unresolvable event. Fixes https://github.com/matrix-org/synapse/issues/11091 and https://github.com/matrix-org/synapse/issues/10764
4. We no longer find connected insertion events by finding a potential `prev_event` connection to the current event we're iterating over. We now solely rely on marker events which when processed, add the insertion event as an extremity and the federating homeserver can ask about it when time calls.
- Related discussion, https://github.com/matrix-org/synapse/pull/11114#discussion_r741514793
Before | After
--- | ---
 | 
#### Why aren't we sorting topologically when receiving backfill events?
> The main reason we're going to opt to not sort topologically when receiving backfill events is because it's probably best to do whatever is easiest to make it just work. People will probably have opinions once they look at [MSC2716](https://github.com/matrix-org/matrix-doc/pull/2716) which could change whatever implementation anyway.
>
> As mentioned, ideally we would do this but code necessary to make the fake edges but it gets confusing and gives an impression of “just whyyyy” (feels icky). This problem also dissolves with online topological ordering.
>
> -- https://github.com/matrix-org/synapse/pull/11114#discussion_r741517138
See https://github.com/matrix-org/synapse/pull/11114#discussion_r739610091 for the technical difficulties
2022-02-07 22:54:13 +01:00
|
|
|
room_id
|
|
|
|
|
)
|
2022-04-26 11:27:11 +02:00
|
|
|
]
|

Add support for MSC2716 marker events (#10498)
* Make historical messages available to federated servers
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
Follow-up to https://github.com/matrix-org/synapse/pull/9247
* Debug message not available on federation
* Add base starting insertion point when no chunk ID is provided
* Fix messages from multiple senders in historical chunk
Follow-up to https://github.com/matrix-org/synapse/pull/9247
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
---
Previously, Synapse would throw a 403,
`Cannot force another user to join.`,
because we were trying to use `?user_id` from a single virtual user
which did not match with messages from other users in the chunk.
* Remove debug lines
* Messing with selecting insertion event extremeties
* Move db schema change to new version
* Add more better comments
* Make a fake requester with just what we need
See https://github.com/matrix-org/synapse/pull/10276#discussion_r660999080
* Store insertion events in table
* Make base insertion event float off on its own
See https://github.com/matrix-org/synapse/pull/10250#issuecomment-875711889
Conflicts:
synapse/rest/client/v1/room.py
* Validate that the app service can actually control the given user
See https://github.com/matrix-org/synapse/pull/10276#issuecomment-876316455
Conflicts:
synapse/rest/client/v1/room.py
* Add some better comments on what we're trying to check for
* Continue debugging
* Share validation logic
* Add inserted historical messages to /backfill response
* Remove debug sql queries
* Some marker event implemntation trials
* Clean up PR
* Rename insertion_event_id to just event_id
* Add some better sql comments
* More accurate description
* Add changelog
* Make it clear what MSC the change is part of
* Add more detail on which insertion event came through
* Address review and improve sql queries
* Only use event_id as unique constraint
* Fix test case where insertion event is already in the normal DAG
* Remove debug changes
* Add support for MSC2716 marker events
* Process markers when we receive it over federation
* WIP: make hs2 backfill historical messages after marker event
* hs2 to better ask for insertion event extremity
But running into the `sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group`
error
* Add insertion_event_extremities table
* Switch to chunk events so we can auth via power_levels
Previously, we were using `content.chunk_id` to connect one
chunk to another. But these events can be from any `sender`
and we can't tell who should be able to send historical events.
We know we only want the application service to do it but these
events have the sender of a real historical message, not the
application service user ID as the sender. Other federated homeservers
also have no indicator which senders are an application service on
the originating homeserver.
So we want to auth all of the MSC2716 events via power_levels
and have them be sent by the application service with proper
PL levels in the room.
* Switch to chunk events for federation
* Add unstable room version to support new historical PL
* Messy: Fix undefined state_group for federated historical events
```
2021-07-13 02:27:57,810 - synapse.handlers.federation - 1248 - ERROR - GET-4 - Failed to backfill from hs1 because NOT NULL constraint failed: event_to_state_groups.state_group
Traceback (most recent call last):
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1216, in try_backfill
await self.backfill(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1035, in backfill
await self._auth_and_persist_event(dest, event, context, backfilled=True)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2222, in _auth_and_persist_event
await self._run_push_actions_and_persist_event(event, context, backfilled)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2244, in _run_push_actions_and_persist_event
await self.persist_events_and_notify(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 3290, in persist_events_and_notify
events, max_stream_token = await self.storage.persistence.persist_events(
File "/usr/local/lib/python3.8/site-packages/synapse/logging/opentracing.py", line 774, in _trace_inner
return await func(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 320, in persist_events
ret_vals = await yieldable_gather_results(enqueue, partitioned.items())
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 237, in handle_queue_loop
ret = await self._per_item_callback(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 577, in _persist_event_batch
await self.persist_events_store._persist_events_and_state_updates(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 176, in _persist_events_and_state_updates
await self.db_pool.runInteraction(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 681, in runInteraction
result = await self.runWithConnection(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 770, in runWithConnection
return await make_deferred_yieldable(
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 238, in inContext
result = inContext.theWork() # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 254, in <lambda>
inContext.theWork = lambda: context.call( # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 118, in callWithContext
return self.currentContext().callWithContext(ctx, func, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 83, in callWithContext
return func(*args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 293, in _runWithConnection
compat.reraise(excValue, excTraceback)
File "/usr/local/lib/python3.8/site-packages/twisted/python/deprecate.py", line 298, in deprecatedFunction
return function(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/twisted/python/compat.py", line 403, in reraise
raise exception.with_traceback(traceback)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 284, in _runWithConnection
result = func(conn, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 765, in inner_func
return func(db_conn, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 549, in new_transaction
r = func(cursor, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/logging/utils.py", line 69, in wrapped
return f(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 385, in _persist_events_txn
self._store_event_state_mappings_txn(txn, events_and_contexts)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 2065, in _store_event_state_mappings_txn
self.db_pool.simple_insert_many_txn(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 923, in simple_insert_many_txn
txn.execute_batch(sql, vals)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 280, in execute_batch
self.executemany(sql, args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 300, in executemany
self._do_execute(self.txn.executemany, sql, *args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 330, in _do_execute
return func(sql, *args)
sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group
```
* Revert "Messy: Fix undefined state_group for federated historical events"
This reverts commit 187ab28611546321e02770944c86f30ee2bc742a.
* Fix federated events being rejected for no state_groups
Add fix from https://github.com/matrix-org/synapse/pull/10439
until it merges.
* Adapting to experimental room version
* Some log cleanup
* Add better comments around extremity fetching code and why
* Rename to be more accurate to what the function returns
* Add changelog
* Ignore rejected events
* Use simplified upsert
* Add Erik's explanation of extra event checks
See https://github.com/matrix-org/synapse/pull/10498#discussion_r680880332
* Clarify that the depth is not directly correlated to the backwards extremity that we return
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681725404
* lock only matters for sqlite
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681728061
* Move new SQL changes to its own delta file
* Clean up upsert docstring
* Bump database schema version (62)
2021-08-04 19:07:57 +02:00
|
|
|
logger.debug(
|
2022-04-26 11:27:11 +02:00
|
|
|
"_maybe_backfill_inner: backwards_extremities=%s insertion_events_to_be_backfilled=%s",
|
|
|
|
|
backwards_extremities,
|

Add support for MSC2716 marker events (#10498)
* Make historical messages available to federated servers
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
Follow-up to https://github.com/matrix-org/synapse/pull/9247
* Debug message not available on federation
* Add base starting insertion point when no chunk ID is provided
* Fix messages from multiple senders in historical chunk
Follow-up to https://github.com/matrix-org/synapse/pull/9247
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
---
Previously, Synapse would throw a 403,
`Cannot force another user to join.`,
because we were trying to use `?user_id` from a single virtual user
which did not match with messages from other users in the chunk.
* Remove debug lines
* Messing with selecting insertion event extremeties
* Move db schema change to new version
* Add more better comments
* Make a fake requester with just what we need
See https://github.com/matrix-org/synapse/pull/10276#discussion_r660999080
* Store insertion events in table
* Make base insertion event float off on its own
See https://github.com/matrix-org/synapse/pull/10250#issuecomment-875711889
Conflicts:
synapse/rest/client/v1/room.py
* Validate that the app service can actually control the given user
See https://github.com/matrix-org/synapse/pull/10276#issuecomment-876316455
Conflicts:
synapse/rest/client/v1/room.py
* Add some better comments on what we're trying to check for
* Continue debugging
* Share validation logic
* Add inserted historical messages to /backfill response
* Remove debug sql queries
* Some marker event implemntation trials
* Clean up PR
* Rename insertion_event_id to just event_id
* Add some better sql comments
* More accurate description
* Add changelog
* Make it clear what MSC the change is part of
* Add more detail on which insertion event came through
* Address review and improve sql queries
* Only use event_id as unique constraint
* Fix test case where insertion event is already in the normal DAG
* Remove debug changes
* Add support for MSC2716 marker events
* Process markers when we receive it over federation
* WIP: make hs2 backfill historical messages after marker event
* hs2 to better ask for insertion event extremity
But running into the `sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group`
error
* Add insertion_event_extremities table
* Switch to chunk events so we can auth via power_levels
Previously, we were using `content.chunk_id` to connect one
chunk to another. But these events can be from any `sender`
and we can't tell who should be able to send historical events.
We know we only want the application service to do it but these
events have the sender of a real historical message, not the
application service user ID as the sender. Other federated homeservers
also have no indicator which senders are an application service on
the originating homeserver.
So we want to auth all of the MSC2716 events via power_levels
and have them be sent by the application service with proper
PL levels in the room.
* Switch to chunk events for federation
* Add unstable room version to support new historical PL
* Messy: Fix undefined state_group for federated historical events
```
2021-07-13 02:27:57,810 - synapse.handlers.federation - 1248 - ERROR - GET-4 - Failed to backfill from hs1 because NOT NULL constraint failed: event_to_state_groups.state_group
Traceback (most recent call last):
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1216, in try_backfill
await self.backfill(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1035, in backfill
await self._auth_and_persist_event(dest, event, context, backfilled=True)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2222, in _auth_and_persist_event
await self._run_push_actions_and_persist_event(event, context, backfilled)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2244, in _run_push_actions_and_persist_event
await self.persist_events_and_notify(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 3290, in persist_events_and_notify
events, max_stream_token = await self.storage.persistence.persist_events(
File "/usr/local/lib/python3.8/site-packages/synapse/logging/opentracing.py", line 774, in _trace_inner
return await func(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 320, in persist_events
ret_vals = await yieldable_gather_results(enqueue, partitioned.items())
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 237, in handle_queue_loop
ret = await self._per_item_callback(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 577, in _persist_event_batch
await self.persist_events_store._persist_events_and_state_updates(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 176, in _persist_events_and_state_updates
await self.db_pool.runInteraction(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 681, in runInteraction
result = await self.runWithConnection(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 770, in runWithConnection
return await make_deferred_yieldable(
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 238, in inContext
result = inContext.theWork() # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 254, in <lambda>
inContext.theWork = lambda: context.call( # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 118, in callWithContext
return self.currentContext().callWithContext(ctx, func, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 83, in callWithContext
return func(*args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 293, in _runWithConnection
compat.reraise(excValue, excTraceback)
File "/usr/local/lib/python3.8/site-packages/twisted/python/deprecate.py", line 298, in deprecatedFunction
return function(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/twisted/python/compat.py", line 403, in reraise
raise exception.with_traceback(traceback)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 284, in _runWithConnection
result = func(conn, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 765, in inner_func
return func(db_conn, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 549, in new_transaction
r = func(cursor, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/logging/utils.py", line 69, in wrapped
return f(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 385, in _persist_events_txn
self._store_event_state_mappings_txn(txn, events_and_contexts)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 2065, in _store_event_state_mappings_txn
self.db_pool.simple_insert_many_txn(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 923, in simple_insert_many_txn
txn.execute_batch(sql, vals)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 280, in execute_batch
self.executemany(sql, args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 300, in executemany
self._do_execute(self.txn.executemany, sql, *args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 330, in _do_execute
return func(sql, *args)
sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group
```
* Revert "Messy: Fix undefined state_group for federated historical events"
This reverts commit 187ab28611546321e02770944c86f30ee2bc742a.
* Fix federated events being rejected for no state_groups
Add fix from https://github.com/matrix-org/synapse/pull/10439
until it merges.
* Adapting to experimental room version
* Some log cleanup
* Add better comments around extremity fetching code and why
* Rename to be more accurate to what the function returns
* Add changelog
* Ignore rejected events
* Use simplified upsert
* Add Erik's explanation of extra event checks
See https://github.com/matrix-org/synapse/pull/10498#discussion_r680880332
* Clarify that the depth is not directly correlated to the backwards extremity that we return
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681725404
* lock only matters for sqlite
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681728061
* Move new SQL changes to its own delta file
* Clean up upsert docstring
* Bump database schema version (62)
2021-08-04 19:07:57 +02:00
|
|
|
insertion_events_to_be_backfilled,
|
|
|
|
|
)
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
if not backwards_extremities and not insertion_events_to_be_backfilled:
|
2015-05-12 11:35:45 +02:00
|
|
|
logger.debug("Not backfilling as no extremeties found.")
|
2020-09-18 15:25:52 +02:00
|
|
|
return False
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
# we now have a list of potential places to backpaginate from. We prefer to
|
|
|
|
|
# start with the most recent (ie, max depth), so let's sort the list.
|
|
|
|
|
sorted_backfill_points: List[_BackfillPoint] = sorted(
|
|
|
|
|
itertools.chain(
|
|
|
|
|
backwards_extremities,
|
|
|
|
|
insertion_events_to_be_backfilled,
|
|
|
|
|
),
|
|
|
|
|
key=lambda e: -int(e.depth),
|
2019-02-20 17:54:35 +01:00
|
|
|
)
|
|
|
|
|
|

Add support for MSC2716 marker events (#10498)
* Make historical messages available to federated servers
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
Follow-up to https://github.com/matrix-org/synapse/pull/9247
* Debug message not available on federation
* Add base starting insertion point when no chunk ID is provided
* Fix messages from multiple senders in historical chunk
Follow-up to https://github.com/matrix-org/synapse/pull/9247
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
---
Previously, Synapse would throw a 403,
`Cannot force another user to join.`,
because we were trying to use `?user_id` from a single virtual user
which did not match with messages from other users in the chunk.
* Remove debug lines
* Messing with selecting insertion event extremeties
* Move db schema change to new version
* Add more better comments
* Make a fake requester with just what we need
See https://github.com/matrix-org/synapse/pull/10276#discussion_r660999080
* Store insertion events in table
* Make base insertion event float off on its own
See https://github.com/matrix-org/synapse/pull/10250#issuecomment-875711889
Conflicts:
synapse/rest/client/v1/room.py
* Validate that the app service can actually control the given user
See https://github.com/matrix-org/synapse/pull/10276#issuecomment-876316455
Conflicts:
synapse/rest/client/v1/room.py
* Add some better comments on what we're trying to check for
* Continue debugging
* Share validation logic
* Add inserted historical messages to /backfill response
* Remove debug sql queries
* Some marker event implemntation trials
* Clean up PR
* Rename insertion_event_id to just event_id
* Add some better sql comments
* More accurate description
* Add changelog
* Make it clear what MSC the change is part of
* Add more detail on which insertion event came through
* Address review and improve sql queries
* Only use event_id as unique constraint
* Fix test case where insertion event is already in the normal DAG
* Remove debug changes
* Add support for MSC2716 marker events
* Process markers when we receive it over federation
* WIP: make hs2 backfill historical messages after marker event
* hs2 to better ask for insertion event extremity
But running into the `sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group`
error
* Add insertion_event_extremities table
* Switch to chunk events so we can auth via power_levels
Previously, we were using `content.chunk_id` to connect one
chunk to another. But these events can be from any `sender`
and we can't tell who should be able to send historical events.
We know we only want the application service to do it but these
events have the sender of a real historical message, not the
application service user ID as the sender. Other federated homeservers
also have no indicator which senders are an application service on
the originating homeserver.
So we want to auth all of the MSC2716 events via power_levels
and have them be sent by the application service with proper
PL levels in the room.
* Switch to chunk events for federation
* Add unstable room version to support new historical PL
* Messy: Fix undefined state_group for federated historical events
```
2021-07-13 02:27:57,810 - synapse.handlers.federation - 1248 - ERROR - GET-4 - Failed to backfill from hs1 because NOT NULL constraint failed: event_to_state_groups.state_group
Traceback (most recent call last):
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1216, in try_backfill
await self.backfill(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1035, in backfill
await self._auth_and_persist_event(dest, event, context, backfilled=True)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2222, in _auth_and_persist_event
await self._run_push_actions_and_persist_event(event, context, backfilled)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2244, in _run_push_actions_and_persist_event
await self.persist_events_and_notify(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 3290, in persist_events_and_notify
events, max_stream_token = await self.storage.persistence.persist_events(
File "/usr/local/lib/python3.8/site-packages/synapse/logging/opentracing.py", line 774, in _trace_inner
return await func(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 320, in persist_events
ret_vals = await yieldable_gather_results(enqueue, partitioned.items())
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 237, in handle_queue_loop
ret = await self._per_item_callback(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 577, in _persist_event_batch
await self.persist_events_store._persist_events_and_state_updates(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 176, in _persist_events_and_state_updates
await self.db_pool.runInteraction(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 681, in runInteraction
result = await self.runWithConnection(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 770, in runWithConnection
return await make_deferred_yieldable(
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 238, in inContext
result = inContext.theWork() # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 254, in <lambda>
inContext.theWork = lambda: context.call( # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 118, in callWithContext
return self.currentContext().callWithContext(ctx, func, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 83, in callWithContext
return func(*args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 293, in _runWithConnection
compat.reraise(excValue, excTraceback)
File "/usr/local/lib/python3.8/site-packages/twisted/python/deprecate.py", line 298, in deprecatedFunction
return function(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/twisted/python/compat.py", line 403, in reraise
raise exception.with_traceback(traceback)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 284, in _runWithConnection
result = func(conn, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 765, in inner_func
return func(db_conn, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 549, in new_transaction
r = func(cursor, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/logging/utils.py", line 69, in wrapped
return f(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 385, in _persist_events_txn
self._store_event_state_mappings_txn(txn, events_and_contexts)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 2065, in _store_event_state_mappings_txn
self.db_pool.simple_insert_many_txn(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 923, in simple_insert_many_txn
txn.execute_batch(sql, vals)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 280, in execute_batch
self.executemany(sql, args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 300, in executemany
self._do_execute(self.txn.executemany, sql, *args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 330, in _do_execute
return func(sql, *args)
sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group
```
* Revert "Messy: Fix undefined state_group for federated historical events"
This reverts commit 187ab28611546321e02770944c86f30ee2bc742a.
* Fix federated events being rejected for no state_groups
Add fix from https://github.com/matrix-org/synapse/pull/10439
until it merges.
* Adapting to experimental room version
* Some log cleanup
* Add better comments around extremity fetching code and why
* Rename to be more accurate to what the function returns
* Add changelog
* Ignore rejected events
* Use simplified upsert
* Add Erik's explanation of extra event checks
See https://github.com/matrix-org/synapse/pull/10498#discussion_r680880332
* Clarify that the depth is not directly correlated to the backwards extremity that we return
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681725404
* lock only matters for sqlite
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681728061
* Move new SQL changes to its own delta file
* Clean up upsert docstring
* Bump database schema version (62)
2021-08-04 19:07:57 +02:00
|
|
|
logger.debug(
|
2022-04-26 11:27:11 +02:00
|
|
|
"_maybe_backfill_inner: room_id: %s: current_depth: %s, limit: %s, "
|
|
|
|
|
"backfill points (%d): %s",
|
|
|
|
|
room_id,
|
|
|
|
|
current_depth,
|
|
|
|
|
limit,
|
|
|
|
|
len(sorted_backfill_points),
|
|
|
|
|
sorted_backfill_points,
|

Add support for MSC2716 marker events (#10498)
* Make historical messages available to federated servers
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
Follow-up to https://github.com/matrix-org/synapse/pull/9247
* Debug message not available on federation
* Add base starting insertion point when no chunk ID is provided
* Fix messages from multiple senders in historical chunk
Follow-up to https://github.com/matrix-org/synapse/pull/9247
Part of MSC2716: https://github.com/matrix-org/matrix-doc/pull/2716
---
Previously, Synapse would throw a 403,
`Cannot force another user to join.`,
because we were trying to use `?user_id` from a single virtual user
which did not match with messages from other users in the chunk.
* Remove debug lines
* Messing with selecting insertion event extremeties
* Move db schema change to new version
* Add more better comments
* Make a fake requester with just what we need
See https://github.com/matrix-org/synapse/pull/10276#discussion_r660999080
* Store insertion events in table
* Make base insertion event float off on its own
See https://github.com/matrix-org/synapse/pull/10250#issuecomment-875711889
Conflicts:
synapse/rest/client/v1/room.py
* Validate that the app service can actually control the given user
See https://github.com/matrix-org/synapse/pull/10276#issuecomment-876316455
Conflicts:
synapse/rest/client/v1/room.py
* Add some better comments on what we're trying to check for
* Continue debugging
* Share validation logic
* Add inserted historical messages to /backfill response
* Remove debug sql queries
* Some marker event implemntation trials
* Clean up PR
* Rename insertion_event_id to just event_id
* Add some better sql comments
* More accurate description
* Add changelog
* Make it clear what MSC the change is part of
* Add more detail on which insertion event came through
* Address review and improve sql queries
* Only use event_id as unique constraint
* Fix test case where insertion event is already in the normal DAG
* Remove debug changes
* Add support for MSC2716 marker events
* Process markers when we receive it over federation
* WIP: make hs2 backfill historical messages after marker event
* hs2 to better ask for insertion event extremity
But running into the `sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group`
error
* Add insertion_event_extremities table
* Switch to chunk events so we can auth via power_levels
Previously, we were using `content.chunk_id` to connect one
chunk to another. But these events can be from any `sender`
and we can't tell who should be able to send historical events.
We know we only want the application service to do it but these
events have the sender of a real historical message, not the
application service user ID as the sender. Other federated homeservers
also have no indicator which senders are an application service on
the originating homeserver.
So we want to auth all of the MSC2716 events via power_levels
and have them be sent by the application service with proper
PL levels in the room.
* Switch to chunk events for federation
* Add unstable room version to support new historical PL
* Messy: Fix undefined state_group for federated historical events
```
2021-07-13 02:27:57,810 - synapse.handlers.federation - 1248 - ERROR - GET-4 - Failed to backfill from hs1 because NOT NULL constraint failed: event_to_state_groups.state_group
Traceback (most recent call last):
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1216, in try_backfill
await self.backfill(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 1035, in backfill
await self._auth_and_persist_event(dest, event, context, backfilled=True)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2222, in _auth_and_persist_event
await self._run_push_actions_and_persist_event(event, context, backfilled)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 2244, in _run_push_actions_and_persist_event
await self.persist_events_and_notify(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 3290, in persist_events_and_notify
events, max_stream_token = await self.storage.persistence.persist_events(
File "/usr/local/lib/python3.8/site-packages/synapse/logging/opentracing.py", line 774, in _trace_inner
return await func(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 320, in persist_events
ret_vals = await yieldable_gather_results(enqueue, partitioned.items())
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 237, in handle_queue_loop
ret = await self._per_item_callback(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/persist_events.py", line 577, in _persist_event_batch
await self.persist_events_store._persist_events_and_state_updates(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 176, in _persist_events_and_state_updates
await self.db_pool.runInteraction(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 681, in runInteraction
result = await self.runWithConnection(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 770, in runWithConnection
return await make_deferred_yieldable(
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 238, in inContext
result = inContext.theWork() # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/threadpool.py", line 254, in <lambda>
inContext.theWork = lambda: context.call( # type: ignore[attr-defined]
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 118, in callWithContext
return self.currentContext().callWithContext(ctx, func, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/python/context.py", line 83, in callWithContext
return func(*args, **kw)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 293, in _runWithConnection
compat.reraise(excValue, excTraceback)
File "/usr/local/lib/python3.8/site-packages/twisted/python/deprecate.py", line 298, in deprecatedFunction
return function(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/twisted/python/compat.py", line 403, in reraise
raise exception.with_traceback(traceback)
File "/usr/local/lib/python3.8/site-packages/twisted/enterprise/adbapi.py", line 284, in _runWithConnection
result = func(conn, *args, **kw)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 765, in inner_func
return func(db_conn, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 549, in new_transaction
r = func(cursor, *args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/logging/utils.py", line 69, in wrapped
return f(*args, **kwargs)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 385, in _persist_events_txn
self._store_event_state_mappings_txn(txn, events_and_contexts)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/databases/main/events.py", line 2065, in _store_event_state_mappings_txn
self.db_pool.simple_insert_many_txn(
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 923, in simple_insert_many_txn
txn.execute_batch(sql, vals)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 280, in execute_batch
self.executemany(sql, args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 300, in executemany
self._do_execute(self.txn.executemany, sql, *args)
File "/usr/local/lib/python3.8/site-packages/synapse/storage/database.py", line 330, in _do_execute
return func(sql, *args)
sqlite3.IntegrityError: NOT NULL constraint failed: event_to_state_groups.state_group
```
* Revert "Messy: Fix undefined state_group for federated historical events"
This reverts commit 187ab28611546321e02770944c86f30ee2bc742a.
* Fix federated events being rejected for no state_groups
Add fix from https://github.com/matrix-org/synapse/pull/10439
until it merges.
* Adapting to experimental room version
* Some log cleanup
* Add better comments around extremity fetching code and why
* Rename to be more accurate to what the function returns
* Add changelog
* Ignore rejected events
* Use simplified upsert
* Add Erik's explanation of extra event checks
See https://github.com/matrix-org/synapse/pull/10498#discussion_r680880332
* Clarify that the depth is not directly correlated to the backwards extremity that we return
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681725404
* lock only matters for sqlite
See https://github.com/matrix-org/synapse/pull/10498#discussion_r681728061
* Move new SQL changes to its own delta file
* Clean up upsert docstring
* Bump database schema version (62)
2021-08-04 19:07:57 +02:00
|
|
|
)
|
2019-02-20 17:54:35 +01:00
|
|
|
|
2020-09-18 15:25:52 +02:00
|
|
|
# If we're approaching an extremity we trigger a backfill, otherwise we
|
|
|
|
|
# no-op.
|
|
|
|
|
#
|
|
|
|
|
# We chose twice the limit here as then clients paginating backwards
|
|
|
|
|
# will send pagination requests that trigger backfill at least twice
|
|
|
|
|
# using the most recent extremity before it gets removed (see below). We
|
|
|
|
|
# chose more than one times the limit in case of failure, but choosing a
|
|
|
|
|
# much larger factor will result in triggering a backfill request much
|
|
|
|
|
# earlier than necessary.
|
2022-04-26 11:27:11 +02:00
|
|
|
#
|
|
|
|
|
# XXX: shouldn't we do this *after* the filter by depth below? Again, we don't
|
|
|
|
|
# care about events that have happened after our current position.
|
|
|
|
|
#
|
|
|
|
|
max_depth = sorted_backfill_points[0].depth
|
2020-09-18 15:25:52 +02:00
|
|
|
if current_depth - 2 * limit > max_depth:
|
|
|
|
|
logger.debug(
|
|
|
|
|
"Not backfilling as we don't need to. %d < %d - 2 * %d",
|
|
|
|
|
max_depth,
|
|
|
|
|
current_depth,
|
|
|
|
|
limit,
|
|
|
|
|
)
|
|
|
|
|
return False
|
|
|
|
|
|
|
|
|
|
# We ignore extremities that have a greater depth than our current depth
|
|
|
|
|
# as:
|
|
|
|
|
# 1. we don't really care about getting events that have happened
|

Fix 500 error on `/messages` when we accumulate more than 5 backward extremities (#11027)
Found while working on the Gitter backfill script and noticed
it only happened after we sent 7 batches, https://gitlab.com/gitterHQ/webapp/-/merge_requests/2229#note_665906390
When there are more than 5 backward extremities for a given depth,
backfill will throw an error because we sliced the extremity list
to 5 but then try to iterate over the full list. This causes
us to look for state that we never fetched and we get a `KeyError`.
Before when calling `/messages` when there are more than 5 backward extremities:
```
Traceback (most recent call last):
File "/usr/local/lib/python3.8/site-packages/synapse/http/server.py", line 258, in _async_render_wrapper
callback_return = await self._async_render(request)
File "/usr/local/lib/python3.8/site-packages/synapse/http/server.py", line 446, in _async_render
callback_return = await raw_callback_return
File "/usr/local/lib/python3.8/site-packages/synapse/rest/client/room.py", line 580, in on_GET
msgs = await self.pagination_handler.get_messages(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/pagination.py", line 396, in get_messages
await self.hs.get_federation_handler().maybe_backfill(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 133, in maybe_backfill
return await self._maybe_backfill_inner(room_id, current_depth, limit)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 386, in _maybe_backfill_inner
likely_extremeties_domains = get_domains_from_state(states[e_id])
KeyError: '$zpFflMEBtZdgcMQWTakaVItTLMjLFdKcRWUPHbbSZJl'
```
2021-10-15 01:53:45 +02:00
|
|
|
# after our current position; and
|
2020-09-18 15:25:52 +02:00
|
|
|
# 2. we have likely previously tried and failed to backfill from that
|
|
|
|
|
# extremity, so to avoid getting "stuck" requesting the same
|
|
|
|
|
# backfill repeatedly we drop those extremities.
|
2022-04-26 11:27:11 +02:00
|
|
|
#
|
2020-09-18 15:25:52 +02:00
|
|
|
# However, we need to check that the filtered extremities are non-empty.
|
|
|
|
|
# If they are empty then either we can a) bail or b) still attempt to
|

Fix 500 error on `/messages` when we accumulate more than 5 backward extremities (#11027)
Found while working on the Gitter backfill script and noticed
it only happened after we sent 7 batches, https://gitlab.com/gitterHQ/webapp/-/merge_requests/2229#note_665906390
When there are more than 5 backward extremities for a given depth,
backfill will throw an error because we sliced the extremity list
to 5 but then try to iterate over the full list. This causes
us to look for state that we never fetched and we get a `KeyError`.
Before when calling `/messages` when there are more than 5 backward extremities:
```
Traceback (most recent call last):
File "/usr/local/lib/python3.8/site-packages/synapse/http/server.py", line 258, in _async_render_wrapper
callback_return = await self._async_render(request)
File "/usr/local/lib/python3.8/site-packages/synapse/http/server.py", line 446, in _async_render
callback_return = await raw_callback_return
File "/usr/local/lib/python3.8/site-packages/synapse/rest/client/room.py", line 580, in on_GET
msgs = await self.pagination_handler.get_messages(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/pagination.py", line 396, in get_messages
await self.hs.get_federation_handler().maybe_backfill(
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 133, in maybe_backfill
return await self._maybe_backfill_inner(room_id, current_depth, limit)
File "/usr/local/lib/python3.8/site-packages/synapse/handlers/federation.py", line 386, in _maybe_backfill_inner
likely_extremeties_domains = get_domains_from_state(states[e_id])
KeyError: '$zpFflMEBtZdgcMQWTakaVItTLMjLFdKcRWUPHbbSZJl'
```
2021-10-15 01:53:45 +02:00
|
|
|
# backfill. We opt to try backfilling anyway just in case we do get
|
2020-09-18 15:25:52 +02:00
|
|
|
# relevant events.
|
2022-04-26 11:27:11 +02:00
|
|
|
#
|
|
|
|
|
filtered_sorted_backfill_points = [
|
|
|
|
|
t for t in sorted_backfill_points if t.depth <= current_depth
|
|
|
|
|
]
|
|
|
|
|
if filtered_sorted_backfill_points:
|
|
|
|
|
logger.debug(
|
|
|
|
|
"_maybe_backfill_inner: backfill points before current depth: %s",
|
|
|
|
|
filtered_sorted_backfill_points,
|
|
|
|
|
)
|
|
|
|
|
sorted_backfill_points = filtered_sorted_backfill_points
|
|
|
|
|
else:
|
|
|
|
|
logger.debug(
|
|
|
|
|
"_maybe_backfill_inner: all backfill points are *after* current depth. Backfilling anyway."
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
# For performance's sake, we only want to paginate from a particular extremity
|
|
|
|
|
# if we can actually see the events we'll get. Otherwise, we'd just spend a lot
|
|
|
|
|
# of resources to get redacted events. We check each extremity in turn and
|
|
|
|
|
# ignore those which users on our server wouldn't be able to see.
|
|
|
|
|
#
|
|
|
|
|
# Additionally, we limit ourselves to backfilling from at most 5 extremities,
|
|
|
|
|
# for two reasons:
|
|
|
|
|
#
|
|
|
|
|
# - The check which determines if we can see an extremity's events can be
|
|
|
|
|
# expensive (we load the full state for the room at each of the backfill
|
|
|
|
|
# points, or (worse) their successors)
|
|
|
|
|
# - We want to avoid the server-server API request URI becoming too long.
|
|
|
|
|
#
|
|
|
|
|
# *Note*: the spec wants us to keep backfilling until we reach the start
|
|
|
|
|
# of the room in case we are allowed to see some of the history. However,
|
|
|
|
|
# in practice that causes more issues than its worth, as (a) it's
|
|
|
|
|
# relatively rare for there to be any visible history and (b) even when
|
|
|
|
|
# there is it's often sufficiently long ago that clients would stop
|
|
|
|
|
# attempting to paginate before backfill reached the visible history.
|
|
|
|
|
|
|
|
|
|
extremities_to_request: List[str] = []
|
|
|
|
|
for bp in sorted_backfill_points:
|
|
|
|
|
if len(extremities_to_request) >= 5:
|
|
|
|
|
break
|
|
|
|
|
|
|
|
|
|
# For regular backwards extremities, we don't have the extremity events
|
|
|
|
|
# themselves, so we need to actually check the events that reference them -
|
|
|
|
|
# their "successor" events.
|
|
|
|
|
#
|
|
|
|
|
# TODO: Correctly handle the case where we are allowed to see the
|
|
|
|
|
# successor event but not the backward extremity, e.g. in the case of
|
|
|
|
|
# initial join of the server where we are allowed to see the join
|
|
|
|
|
# event but not anything before it. This would require looking at the
|
|
|
|
|
# state *before* the event, ignoring the special casing certain event
|
|
|
|
|
# types have.
|
|
|
|
|
if bp.type == _BackfillPointType.INSERTION_PONT:
|
|
|
|
|
event_ids_to_check = [bp.event_id]
|
|
|
|
|
else:
|
|
|
|
|
event_ids_to_check = await self.store.get_successor_events(bp.event_id)
|
|
|
|
|
|
|
|
|
|
events_to_check = await self.store.get_events_as_list(
|
|
|
|
|
event_ids_to_check,
|
|
|
|
|
redact_behaviour=EventRedactBehaviour.AS_IS,
|
|
|
|
|
get_prev_content=False,
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
# We set `check_history_visibility_only` as we might otherwise get false
|
|
|
|
|
# positives from users having been erased.
|
|
|
|
|
filtered_extremities = await filter_events_for_server(
|
|
|
|
|
self.storage,
|
|
|
|
|
self.server_name,
|
|
|
|
|
events_to_check,
|
|
|
|
|
redact=False,
|
|
|
|
|
check_history_visibility_only=True,
|
|
|
|
|
)
|
|
|
|
|
if filtered_extremities:
|
|
|
|
|
extremities_to_request.append(bp.event_id)
|
|
|
|
|
else:
|
|
|
|
|
logger.debug(
|
|
|
|
|
"_maybe_backfill_inner: skipping extremity %s as it would not be visible",
|
|
|
|
|
bp,
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
if not extremities_to_request:
|
|
|
|
|
logger.debug(
|
|
|
|
|
"_maybe_backfill_inner: found no extremities which would be visible"
|
|
|
|
|
)
|
|
|
|
|
return False
|
2020-09-18 15:25:52 +02:00
|
|
|
|
2022-04-26 11:27:11 +02:00
|
|
|
logger.debug(
|
|
|
|
|
"_maybe_backfill_inner: extremities_to_request %s", extremities_to_request
|
|
|
|
|
)
|
2016-08-16 12:34:36 +02:00
|
|
|
|
2015-05-11 19:01:31 +02:00
|
|
|
# Now we need to decide which hosts to hit first.
|
|
|
|
|
|
2015-05-12 11:35:45 +02:00
|
|
|
# First we try hosts that are already in the room
|
|
|
|
|
# TODO: HEURISTIC ALERT.
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2019-12-10 17:54:34 +01:00
|
|
|
curr_state = await self.state_handler.get_current_state(room_id)
|
2015-05-11 19:01:31 +02:00
|
|
|
|
|
|
|
|
curr_domains = get_domains_from_state(curr_state)
|
|
|
|
|
|
|
|
|
|
likely_domains = [
|
2019-06-20 11:32:02 +02:00
|
|
|
domain for domain, depth in curr_domains if domain != self.server_name
|
2015-05-11 19:01:31 +02:00
|
|
|
]
|
|
|
|
|
|
2021-04-06 13:21:57 +02:00
|
|
|
async def try_backfill(domains: List[str]) -> bool:
|
2015-05-11 19:01:31 +02:00
|
|
|
# TODO: Should we try multiple of these at a time?
|
|
|
|
|
for dom in domains:
|
2015-05-12 11:35:45 +02:00
|
|
|
try:
|
2021-08-26 22:41:44 +02:00
|
|
|
await self._federation_event_handler.backfill(
|
2022-04-26 11:27:11 +02:00
|
|
|
dom, room_id, limit=100, extremities=extremities_to_request
|
2015-05-12 11:35:45 +02:00
|
|
|
)
|
2016-04-12 13:04:19 +02:00
|
|
|
# If this succeeded then we probably already have the
|
|
|
|
|
# appropriate stuff.
|
2016-04-12 13:48:30 +02:00
|
|
|
# TODO: We can probably do something more intelligent here.
|
2019-07-23 15:00:55 +02:00
|
|
|
return True
|
2021-08-26 19:34:57 +02:00
|
|
|
except (SynapseError, InvalidResponseError) as e:
|
2020-05-22 12:39:20 +02:00
|
|
|
logger.info("Failed to backfill from %s because %s", dom, e)
|
|
|
|
|
continue
|
|
|
|
|
except HttpResponseException as e:
|
|
|
|
|
if 400 <= e.code < 500:
|
|
|
|
|
raise e.to_synapse_error()
|
|
|
|
|
|
2019-06-20 11:32:02 +02:00
|
|
|
logger.info("Failed to backfill from %s because %s", dom, e)
|
2015-05-12 11:35:45 +02:00
|
|
|
continue
|
|
|
|
|
except CodeMessageException as e:
|
|
|
|
|
if 400 <= e.code < 500:
|
|
|
|
|
raise
|
|
|
|
|
|
2019-06-20 11:32:02 +02:00
|
|
|
logger.info("Failed to backfill from %s because %s", dom, e)
|
2015-05-12 11:35:45 +02:00
|
|
|
continue
|
|
|
|
|
except NotRetryingDestination as e:
|
2018-09-06 16:22:23 +02:00
|
|
|
logger.info(str(e))
|
2015-05-12 11:35:45 +02:00
|
|
|
continue
|
2019-07-30 14:19:22 +02:00
|
|
|
except RequestSendFailed as e:
|
2020-10-23 18:38:40 +02:00
|
|
|
logger.info("Failed to get backfill from %s because %s", dom, e)
|
2019-07-30 14:19:22 +02:00
|
|
|
continue
|
2018-01-22 19:11:18 +01:00
|
|
|
except FederationDeniedError as e:
|
|
|
|
|
logger.info(e)
|
|
|
|
|
continue
|
2015-05-12 11:35:45 +02:00
|
|
|
except Exception as e:
|
2019-06-20 11:32:02 +02:00
|
|
|
logger.exception("Failed to backfill from %s because %s", dom, e)
|
2015-05-12 11:35:45 +02:00
|
|
|
continue
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2019-07-23 15:00:55 +02:00
|
|
|
return False
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2019-12-10 17:54:34 +01:00
|
|
|
success = await try_backfill(likely_domains)
|
2015-05-11 19:01:31 +02:00
|
|
|
if success:
|
2019-07-23 15:00:55 +02:00
|
|
|
return True
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2022-03-09 12:00:48 +01:00
|
|
|
# TODO: we could also try servers which were previously in the room, but
|
|
|
|
|
# are no longer.
|
2015-05-11 19:01:31 +02:00
|
|
|
|
2021-08-26 22:41:44 +02:00
|
|
|
return False
|
2018-04-18 00:41:12 +02:00
|
|
|
|
2021-04-06 13:21:57 +02:00
|
|
|
async def send_invite(self, target_host: str, event: EventBase) -> EventBase:
|
2021-02-16 23:32:34 +01:00
|
|
|
"""Sends the invite to the remote server for signing.
|
2014-11-12 17:20:21 +01:00
|
|
|
|
|
|
|
|
Invites must be signed by the invitee's server before distribution.
|
|
|
|
|
"""
|
2021-07-15 11:35:46 +02:00
|
|
|
try:
|
|
|
|
|
pdu = await self.federation_client.send_invite(
|
|
|
|
|
destination=target_host,
|
|
|
|
|
room_id=event.room_id,
|
|
|
|
|
event_id=event.event_id,
|
|
|
|
|
pdu=event,
|
|
|
|
|
)
|
|
|
|
|
except RequestSendFailed:
|
|
|
|
|
raise SynapseError(502, f"Can't connect to server {target_host}")
|
2014-11-07 14:41:00 +01:00
|
|
|
|
2019-07-23 15:00:55 +02:00
|
|
|
return pdu
|
2014-11-07 14:41:00 +01:00
|
|
|
|
2020-02-03 17:06:46 +01:00
|
|
|
async def on_event_auth(self, event_id: str) -> List[EventBase]:
|
|
|
|
|
event = await self.store.get_event(event_id)
|
|
|
|
|
auth = await self.store.get_auth_chain(
|
2021-03-10 15:57:59 +01:00
|
|
|
event.room_id, list(event.auth_event_ids()), include_given=True
|
2017-05-24 15:22:41 +02:00
|
|
|
)
|
2020-02-03 17:06:46 +01:00
|
|
|
return list(auth)
|
2014-11-07 16:35:53 +01:00
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
async def do_invite_join(
|
|
|
|
|
self, target_hosts: Iterable[str], room_id: str, joinee: str, content: JsonDict
|
2020-05-22 15:21:54 +02:00
|
|
|
) -> Tuple[str, int]:
|
2021-02-16 23:32:34 +01:00
|
|
|
"""Attempts to join the `joinee` to the room `room_id` via the
|
2019-11-01 11:28:09 +01:00
|
|
|
servers contained in `target_hosts`.
|
2014-11-12 17:20:21 +01:00
|
|
|
|
|
|
|
|
This first triggers a /make_join/ request that returns a partial
|
|
|
|
|
event that we can fill out and sign. This is then sent to the
|
|
|
|
|
remote server via /send_join/ which responds with the state at that
|
|
|
|
|
event and the auth_chains.
|
|
|
|
|
|
|
|
|
|
We suspend processing of any received events from this room until we
|
|
|
|
|
have finished processing the join.
|
2019-11-01 11:28:09 +01:00
|
|
|
|
|
|
|
|
Args:
|
2020-02-03 17:13:13 +01:00
|
|
|
target_hosts: List of servers to attempt to join the room with.
|
2019-11-01 11:28:09 +01:00
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
room_id: The ID of the room to join.
|
2019-11-01 11:28:09 +01:00
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
joinee: The User ID of the joining user.
|
2019-11-01 11:28:09 +01:00
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
content: The event content to use for the join event.
|
2014-11-12 17:20:21 +01:00
|
|
|
"""
|
2020-05-22 17:11:35 +02:00
|
|
|
# TODO: We should be able to call this on workers, but the upgrading of
|
|
|
|
|
# room stuff after join currently doesn't work on workers.
|
|
|
|
|
assert self.config.worker.worker_app is None
|
|
|
|
|
|
2014-11-25 12:31:18 +01:00
|
|
|
logger.debug("Joining %s to %s", joinee, room_id)
|
|
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
origin, event, room_version_obj = await self._make_and_verify_event(
|
2015-02-05 14:43:28 +01:00
|
|
|
target_hosts,
|
2014-10-17 16:04:17 +02:00
|
|
|
room_id,
|
2015-10-01 18:49:52 +02:00
|
|
|
joinee,
|
2015-11-12 17:19:55 +01:00
|
|
|
"join",
|
|
|
|
|
content,
|
2019-06-20 11:32:02 +02:00
|
|
|
params={"ver": KNOWN_ROOM_VERSIONS},
|
2014-08-20 15:42:36 +02:00
|
|
|
)
|
|
|
|
|
|
2017-03-14 12:26:57 +01:00
|
|
|
# This shouldn't happen, because the RoomMemberHandler has a
|
|
|
|
|
# linearizer lock which only allows one operation per user per room
|
|
|
|
|
# at a time - so this is just paranoia.
|
2021-08-26 22:41:44 +02:00
|
|
|
assert room_id not in self._federation_event_handler.room_queues
|
2017-03-14 12:26:57 +01:00
|
|
|
|
2021-08-26 22:41:44 +02:00
|
|
|
self._federation_event_handler.room_queues[room_id] = []
|
2017-03-14 12:26:57 +01:00
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
await self._clean_room_for_join(room_id)
|
2017-03-14 12:26:57 +01:00
|
|
|
|
2014-10-29 17:59:24 +01:00
|
|
|
try:
|
2015-02-05 14:43:28 +01:00
|
|
|
# Try the host we successfully got a response to /make_join/
|
|
|
|
|
# request first.
|
2020-07-01 17:21:02 +02:00
|
|
|
host_list = list(target_hosts)
|
2015-02-06 11:53:18 +01:00
|
|
|
try:
|
2020-07-01 17:21:02 +02:00
|
|
|
host_list.remove(origin)
|
|
|
|
|
host_list.insert(0, origin)
|
2015-02-06 11:53:18 +01:00
|
|
|
except ValueError:
|
|
|
|
|
pass
|
2020-01-27 15:30:57 +01:00
|
|
|
|
2020-02-03 17:13:13 +01:00
|
|
|
ret = await self.federation_client.send_join(
|
2020-07-01 17:21:02 +02:00
|
|
|
host_list, event, room_version_obj
|
2019-01-23 21:21:33 +01:00
|
|
|
)
|
2014-10-17 19:56:42 +02:00
|
|
|
|
2021-07-26 18:17:00 +02:00
|
|
|
event = ret.event
|
|
|
|
|
origin = ret.origin
|
|
|
|
|
state = ret.state
|
|
|
|
|
auth_chain = ret.auth_chain
|
2014-11-27 17:02:26 +01:00
|
|
|
auth_chain.sort(key=lambda e: e.depth)
|
2014-08-20 15:42:36 +02:00
|
|
|
|
2014-11-25 12:31:18 +01:00
|
|
|
logger.debug("do_invite_join auth_chain: %s", auth_chain)
|
|
|
|
|
logger.debug("do_invite_join state: %s", state)
|
2014-10-17 19:56:42 +02:00
|
|
|
|
2015-12-10 18:08:21 +01:00
|
|
|
logger.debug("do_invite_join event: %s", event)
|
2014-10-29 17:59:24 +01:00
|
|
|
|
2020-02-24 16:46:41 +01:00
|
|
|
# if this is the first time we've joined this room, it's time to add
|
|
|
|
|
# a row to `rooms` with the correct room version. If there's already a
|
|
|
|
|
# row there, we should override it, since it may have been populated
|
|
|
|
|
# based on an invite request which lied about the room version.
|
|
|
|
|
#
|
|
|
|
|
# federation_client.send_join has already checked that the room
|
|
|
|
|
# version in the received create event is the same as room_version_obj,
|
|
|
|
|
# so we can rely on it now.
|
|
|
|
|
#
|
|
|
|
|
await self.store.upsert_room_on_join(
|
2021-02-16 23:32:34 +01:00
|
|
|
room_id=room_id,
|
|
|
|
|
room_version=room_version_obj,
|
2022-02-21 20:27:35 +01:00
|
|
|
state_events=state,
|
2020-02-24 16:46:41 +01:00
|
|
|
)
|
2014-10-29 17:59:24 +01:00
|
|
|
|
2022-03-01 13:49:54 +01:00
|
|
|
if ret.partial_state:
|
2022-04-12 15:23:43 +02:00
|
|
|
# TODO(faster_joins): roll this back if we don't manage to start the
|
|
|
|
|
# background resync (eg process_remote_join fails)
|
2022-03-01 13:49:54 +01:00
|
|
|
await self.store.store_partial_state_room(room_id, ret.servers_in_room)
|
|
|
|
|
|
2021-10-19 11:24:09 +02:00
|
|
|
max_stream_id = await self._federation_event_handler.process_remote_join(
|
2022-03-01 13:49:54 +01:00
|
|
|
origin,
|
|
|
|
|
room_id,
|
|
|
|
|
auth_chain,
|
|
|
|
|
state,
|
|
|
|
|
event,
|
|
|
|
|
room_version_obj,
|
|
|
|
|
partial_state=ret.partial_state,
|
2020-01-27 15:30:57 +01:00
|
|
|
)
|
2014-10-29 17:59:24 +01:00
|
|
|
|
2022-04-12 15:23:43 +02:00
|
|
|
if ret.partial_state:
|
|
|
|
|
# Kick off the process of asynchronously fetching the state for this
|
|
|
|
|
# room.
|
|
|
|
|
#
|
|
|
|
|
# TODO(faster_joins): pick this up again on restart
|
|
|
|
|
run_as_background_process(
|
|
|
|
|
desc="sync_partial_state_room",
|
|
|
|
|
func=self._sync_partial_state_room,
|
|
|
|
|
destination=origin,
|
|
|
|
|
room_id=room_id,
|
|
|
|
|
)
|
|
|
|
|
|
2020-05-22 15:21:54 +02:00
|
|
|
# We wait here until this instance has seen the events come down
|
|
|
|
|
# replication (if we're using replication) as the below uses caches.
|
|
|
|
|
await self._replication.wait_for_stream_position(
|
2020-09-14 11:16:41 +02:00
|
|
|
self.config.worker.events_shard_config.get_instance(room_id),
|
|
|
|
|
"events",
|
|
|
|
|
max_stream_id,
|
2020-05-22 15:21:54 +02:00
|
|
|
)
|
|
|
|
|
|
2019-11-01 11:28:09 +01:00
|
|
|
# Check whether this room is the result of an upgrade of a room we already know
|
|
|
|
|
# about. If so, migrate over user information
|
2020-02-03 17:13:13 +01:00
|
|
|
predecessor = await self.store.get_room_predecessor(room_id)
|
2019-12-11 14:07:25 +01:00
|
|
|
if not predecessor or not isinstance(predecessor.get("room_id"), str):
|
2020-05-22 15:21:54 +02:00
|
|
|
return event.event_id, max_stream_id
|
2019-11-01 11:28:09 +01:00
|
|
|
old_room_id = predecessor["room_id"]
|
|
|
|
|
logger.debug(
|
|
|
|
|
"Found predecessor for %s during remote join: %s", room_id, old_room_id
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
# We retrieve the room member handler here as to not cause a cyclic dependency
|
|
|
|
|
member_handler = self.hs.get_room_member_handler()
|
2020-02-03 17:13:13 +01:00
|
|
|
await member_handler.transfer_room_state_on_room_upgrade(
|
2019-11-01 11:28:09 +01:00
|
|
|
old_room_id, room_id
|
|
|
|
|
)
|
|
|
|
|
|
2014-11-25 12:31:18 +01:00
|
|
|
logger.debug("Finished joining %s to %s", joinee, room_id)
|
2020-05-22 15:21:54 +02:00
|
|
|
return event.event_id, max_stream_id
|
2014-10-29 17:59:24 +01:00
|
|
|
finally:
|
2021-08-26 22:41:44 +02:00
|
|
|
room_queue = self._federation_event_handler.room_queues[room_id]
|
|
|
|
|
del self._federation_event_handler.room_queues[room_id]
|
2014-10-17 19:56:42 +02:00
|
|
|
|
2017-03-14 12:26:57 +01:00
|
|
|
# we don't need to wait for the queued events to be processed -
|
|
|
|
|
# it's just a best-effort thing at this point. We do want to do
|
|
|
|
|
# them roughly in order, though, otherwise we'll end up making
|
|
|
|
|
# lots of requests for missing prev_events which we do actually
|
2020-07-24 16:53:25 +02:00
|
|
|
# have. Hence we fire off the background task, but don't wait for it.
|
2014-12-10 16:55:03 +01:00
|
|
|
|
2022-02-22 14:33:22 +01:00
|
|
|
run_as_background_process(
|
|
|
|
|
"handle_queued_pdus", self._handle_queued_pdus, room_queue
|
|
|
|
|
)
|
2014-10-17 19:56:42 +02:00
|
|
|
|
2021-06-09 20:39:51 +02:00
|
|
|
async def do_knock(
|
|
|
|
|
self,
|
|
|
|
|
target_hosts: List[str],
|
|
|
|
|
room_id: str,
|
|
|
|
|
knockee: str,
|
|
|
|
|
content: JsonDict,
|
|
|
|
|
) -> Tuple[str, int]:
|
|
|
|
|
"""Sends the knock to the remote server.
|
|
|
|
|
|
|
|
|
|
This first triggers a make_knock request that returns a partial
|
|
|
|
|
event that we can fill out and sign. This is then sent to the
|
|
|
|
|
remote server via send_knock.
|
|
|
|
|
|
|
|
|
|
Knock events must be signed by the knockee's server before distributing.
|
|
|
|
|
|
|
|
|
|
Args:
|
|
|
|
|
target_hosts: A list of hosts that we want to try knocking through.
|
|
|
|
|
room_id: The ID of the room to knock on.
|
|
|
|
|
knockee: The ID of the user who is knocking.
|
|
|
|
|
content: The content of the knock event.
|
|
|
|
|
|
|
|
|
|
Returns:
|
|
|
|
|
A tuple of (event ID, stream ID).
|
|
|
|
|
|
|
|
|
|
Raises:
|
|
|
|
|
SynapseError: If the chosen remote server returns a 3xx/4xx code.
|
|
|
|
|
RuntimeError: If no servers were reachable.
|
|
|
|
|
"""
|
|
|
|
|
logger.debug("Knocking on room %s on behalf of user %s", room_id, knockee)
|
|
|
|
|
|
|
|
|
|
# Inform the remote server of the room versions we support
|
|
|
|
|
supported_room_versions = list(KNOWN_ROOM_VERSIONS.keys())
|
|
|
|
|
|
|
|
|
|
# Ask the remote server to create a valid knock event for us. Once received,
|
|
|
|
|
# we sign the event
|
2021-07-16 19:22:36 +02:00
|
|
|
params: Dict[str, Iterable[str]] = {"ver": supported_room_versions}
|
2021-06-09 20:39:51 +02:00
|
|
|
origin, event, event_format_version = await self._make_and_verify_event(
|
|
|
|
|
target_hosts, room_id, knockee, Membership.KNOCK, content, params=params
|
|
|
|
|
)
|
|
|
|
|
|
2021-09-22 16:20:18 +02:00
|
|
|
# Mark the knock as an outlier as we don't yet have the state at this point in
|
|
|
|
|
# the DAG.
|
|
|
|
|
event.internal_metadata.outlier = True
|
|
|
|
|
|
|
|
|
|
# ... but tell /sync to send it to clients anyway.
|
|
|
|
|
event.internal_metadata.out_of_band_membership = True
|
|
|
|
|
|
2021-06-09 20:39:51 +02:00
|
|
|
# Record the room ID and its version so that we have a record of the room
|
|
|
|
|
await self._maybe_store_room_on_outlier_membership(
|
|
|
|
|
room_id=event.room_id, room_version=event_format_version
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
# Initially try the host that we successfully called /make_knock on
|
|
|
|
|
try:
|
|
|
|
|
target_hosts.remove(origin)
|
|
|
|
|
target_hosts.insert(0, origin)
|
|
|
|
|
except ValueError:
|
|
|
|
|
pass
|
|
|
|
|
|
|
|
|
|
# Send the signed event back to the room, and potentially receive some
|
|
|
|
|
# further information about the room in the form of partial state events
|
|
|
|
|
stripped_room_state = await self.federation_client.send_knock(
|
|
|
|
|
target_hosts, event
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
# Store any stripped room state events in the "unsigned" key of the event.
|
|
|
|
|
# This is a bit of a hack and is cribbing off of invites. Basically we
|
|
|
|
|
# store the room state here and retrieve it again when this event appears
|
|
|
|
|
# in the invitee's sync stream. It is stripped out for all other local users.
|
|
|
|
|
event.unsigned["knock_room_state"] = stripped_room_state["knock_state_events"]
|
|
|
|
|
|
2021-09-22 18:58:57 +02:00
|
|
|
context = EventContext.for_outlier()
|
2021-08-26 22:41:44 +02:00
|
|
|
stream_id = await self._federation_event_handler.persist_events_and_notify(
|
2021-06-09 20:39:51 +02:00
|
|
|
event.room_id, [(event, context)]
|
|
|
|
|
)
|
|
|
|
|
return event.event_id, stream_id
|
|
|
|
|
|
2021-04-06 13:21:57 +02:00
|
|
|
async def _handle_queued_pdus(
|
|
|
|
|
self, room_queue: List[Tuple[EventBase, str]]
|
|
|
|
|
) -> None:
|
2017-03-14 12:26:57 +01:00
|
|
|
"""Process PDUs which got queued up while we were busy send_joining.
|
|
|
|
|
|
|
|
|
|
Args:
|
2021-04-06 13:21:57 +02:00
|
|
|
room_queue: list of PDUs to be processed and the servers that sent them
|
2017-03-14 12:26:57 +01:00
|
|
|
"""
|
|
|
|
|
for p, origin in room_queue:
|
|
|
|
|
try:
|
2019-06-20 11:32:02 +02:00
|
|
|
logger.info(
|
2021-08-16 14:19:02 +02:00
|
|
|
"Processing queued PDU %s which was received while we were joining",
|
|
|
|
|
p,
|
2019-06-20 11:32:02 +02:00
|
|
|
)
|
2019-07-03 16:07:04 +02:00
|
|
|
with nested_logging_context(p.event_id):
|
2021-08-26 22:41:44 +02:00
|
|
|
await self._federation_event_handler.on_receive_pdu(origin, p)
|
2017-03-14 12:26:57 +01:00
|
|
|
except Exception as e:
|
2019-10-31 11:23:24 +01:00
|
|
|
logger.warning(
|
2019-06-20 11:32:02 +02:00
|
|
|
"Error handling queued PDU %s from %s: %s", p.event_id, origin, e
|
|
|
|
|
)
|
2017-03-14 12:26:57 +01:00
|
|
|
|
2020-02-03 16:35:30 +01:00
|
|
|
async def on_make_join_request(
|
|
|
|
|
self, origin: str, room_id: str, user_id: str
|
|
|
|
|
) -> EventBase:
|
2021-02-16 23:32:34 +01:00
|
|
|
"""We've received a /make_join/ request, so we create a partial
|
2015-10-20 12:58:58 +02:00
|
|
|
join event for the room and return that. We do *not* persist or
|
2014-11-12 17:20:21 +01:00
|
|
|
process it until the other server has signed it and sent it back.
|
2019-07-26 11:08:22 +02:00
|
|
|
|
|
|
|
|
Args:
|
2020-02-03 16:35:30 +01:00
|
|
|
origin: The (verified) server name of the requesting server.
|
|
|
|
|
room_id: Room to create join event in
|
|
|
|
|
user_id: The user to create the join for
|
2014-11-12 17:20:21 +01:00
|
|
|
"""
|
2019-07-26 11:08:22 +02:00
|
|
|
if get_domain_from_id(user_id) != origin:
|
|
|
|
|
logger.info(
|
|
|
|
|
"Got /make_join request for user %r from different origin %s, ignoring",
|
|
|
|
|
user_id,
|
|
|
|
|
origin,
|
|
|
|
|
)
|
|
|
|
|
raise SynapseError(403, "User not from origin", Codes.FORBIDDEN)
|
|
|
|
|
|
2020-07-16 16:17:31 +02:00
|
|
|
# checking the room version will check that we've actually heard of the room
|
|
|
|
|
# (and return a 404 otherwise)
|
2021-07-26 18:17:00 +02:00
|
|
|
room_version = await self.store.get_room_version(room_id)
|
2019-01-23 21:21:33 +01:00
|
|
|
|
2020-07-16 16:17:31 +02:00
|
|
|
# now check that we are *still* in the room
|
2021-07-01 20:25:37 +02:00
|
|
|
is_in_room = await self._event_auth_handler.check_host_in_room(
|
|
|
|
|
room_id, self.server_name
|
|
|
|
|
)
|
2020-07-16 16:17:31 +02:00
|
|
|
if not is_in_room:
|
|
|
|
|
logger.info(
|
2021-02-16 23:32:34 +01:00
|
|
|
"Got /make_join request for room %s we are no longer in",
|
|
|
|
|
room_id,
|
2020-07-16 16:17:31 +02:00
|
|
|
)
|
|
|
|
|
raise NotFoundError("Not an active room on this server")
|
|
|
|
|
|
|
|
|
|
event_content = {"membership": Membership.JOIN}
|
|
|
|
|
|
2021-07-26 18:17:00 +02:00
|
|
|
# If the current room is using restricted join rules, additional information
|
|
|
|
|
# may need to be included in the event content in order to efficiently
|
|
|
|
|
# validate the event.
|
|
|
|
|
#
|
|
|
|
|
# Note that this requires the /send_join request to come back to the
|
|
|
|
|
# same server.
|
|
|
|
|
if room_version.msc3083_join_rules:
|
|
|
|
|
state_ids = await self.store.get_current_state_ids(room_id)
|
|
|
|
|
if await self._event_auth_handler.has_restricted_join_rules(
|
|
|
|
|
state_ids, room_version
|
|
|
|
|
):
|
|
|
|
|
prev_member_event_id = state_ids.get((EventTypes.Member, user_id), None)
|
|
|
|
|
# If the user is invited or joined to the room already, then
|
|
|
|
|
# no additional info is needed.
|
|
|
|
|
include_auth_user_id = True
|
|
|
|
|
if prev_member_event_id:
|
|
|
|
|
prev_member_event = await self.store.get_event(prev_member_event_id)
|
|
|
|
|
include_auth_user_id = prev_member_event.membership not in (
|
|
|
|
|
Membership.JOIN,
|
|
|
|
|
Membership.INVITE,
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
if include_auth_user_id:
|
|
|
|
|
event_content[
|
2021-09-30 17:13:59 +02:00
|
|
|
EventContentFields.AUTHORISING_USER
|
2021-07-26 18:17:00 +02:00
|
|
|
] = await self._event_auth_handler.get_user_which_could_invite(
|
|
|
|
|
room_id,
|
|
|
|
|
state_ids,
|
|
|
|
|
)
|
|
|
|
|
|
2021-09-29 11:57:10 +02:00
|
|
|
builder = self.event_builder_factory.for_room_version(
|
|
|
|
|
room_version,
|
2019-01-23 21:21:33 +01:00
|
|
|
{
|
|
|
|
|
"type": EventTypes.Member,
|
|
|
|
|
"content": event_content,
|
|
|
|
|
"room_id": room_id,
|
|
|
|
|
"sender": user_id,
|
|
|
|
|
"state_key": user_id,
|
2019-06-20 11:32:02 +02:00
|
|
|
},
|
2019-01-23 21:21:33 +01:00
|
|
|
)
|
2014-12-04 16:50:01 +01:00
|
|
|
|
2016-04-13 12:11:46 +02:00
|
|
|
try:
|
2020-02-03 16:35:30 +01:00
|
|
|
event, context = await self.event_creation_handler.create_new_client_event(
|
2019-06-20 11:32:02 +02:00
|
|
|
builder=builder
|
2016-04-13 12:11:46 +02:00
|
|
|
)
|
2020-10-13 16:44:54 +02:00
|
|
|
except SynapseError as e:
|
2019-10-31 11:23:24 +01:00
|
|
|
logger.warning("Failed to create join to %s because %s", room_id, e)
|
2020-10-13 16:44:54 +02:00
|
|
|
raise
|
2019-06-12 11:31:37 +02:00
|
|
|
|
2021-07-26 18:17:00 +02:00
|
|
|
# Ensure the user can even join the room.
|
2021-08-26 22:41:44 +02:00
|
|
|
await self._federation_event_handler.check_join_restrictions(context, event)
|
2021-07-26 18:17:00 +02:00
|
|
|
|
2016-07-15 10:29:54 +02:00
|
|
|
# The remote hasn't signed it yet, obviously. We'll do the full checks
|
|
|
|
|
# when we get the event back in `on_send_join_request`
|
Split `event_auth.check` into two parts (#10940)
Broadly, the existing `event_auth.check` function has two parts:
* a validation section: checks that the event isn't too big, that it has the rught signatures, etc.
This bit is independent of the rest of the state in the room, and so need only be done once
for each event.
* an auth section: ensures that the event is allowed, given the rest of the state in the room.
This gets done multiple times, against various sets of room state, because it forms part of
the state res algorithm.
Currently, this is implemented with `do_sig_check` and `do_size_check` parameters, but I think
that makes everything hard to follow. Instead, we split the function in two and call each part
separately where it is needed.
2021-09-29 19:59:15 +02:00
|
|
|
await self._event_auth_handler.check_auth_rules_from_context(
|
|
|
|
|
room_version, event, context
|
2019-01-25 19:31:41 +01:00
|
|
|
)
|
2019-07-23 15:00:55 +02:00
|
|
|
return event
|
2014-10-16 17:56:51 +02:00
|
|
|
|
2020-02-03 16:33:42 +01:00
|
|
|
async def on_invite_request(
|
2020-01-30 23:13:02 +01:00
|
|
|
self, origin: str, event: EventBase, room_version: RoomVersion
|
2021-04-06 13:21:57 +02:00
|
|
|
) -> EventBase:
|
2021-02-16 23:32:34 +01:00
|
|
|
"""We've got an invite event. Process and persist it. Sign it.
|
2014-11-12 17:20:21 +01:00
|
|
|
|
|
|
|
|
Respond with the now signed event.
|
|
|
|
|
"""
|
2017-10-05 15:02:28 +02:00
|
|
|
if event.state_key is None:
|
|
|
|
|
raise SynapseError(400, "The invite event did not have a state key")
|
|
|
|
|
|
2020-02-03 16:33:42 +01:00
|
|
|
is_blocked = await self.store.is_room_blocked(event.room_id)
|
2017-06-19 13:36:28 +02:00
|
|
|
if is_blocked:
|
|
|
|
|
raise SynapseError(403, "This room has been blocked on this server")
|
|
|
|
|
|
2021-09-29 12:44:15 +02:00
|
|
|
if self.hs.config.server.block_non_admin_invites:
|
2017-09-19 17:08:14 +02:00
|
|
|
raise SynapseError(403, "This server does not accept room invites")
|
|
|
|
|
|
2020-12-11 20:05:15 +01:00
|
|
|
if not await self.spam_checker.user_may_invite(
|
2019-06-20 11:32:02 +02:00
|
|
|
event.sender, event.state_key, event.room_id
|
2017-10-05 15:02:28 +02:00
|
|
|
):
|
2017-10-03 15:04:10 +02:00
|
|
|
raise SynapseError(
|
2017-10-05 15:02:28 +02:00
|
|
|
403, "This user is not permitted to send invites to this server/user"
|
2017-10-03 15:04:10 +02:00
|
|
|
)
|
2017-10-03 14:53:09 +02:00
|
|
|
|
2017-06-30 17:20:30 +02:00
|
|
|
membership = event.content.get("membership")
|
|
|
|
|
if event.type != EventTypes.Member or membership != Membership.INVITE:
|
|
|
|
|
raise SynapseError(400, "The event was not an m.room.member invite event")
|
|
|
|
|
|
|
|
|
|
sender_domain = get_domain_from_id(event.sender)
|
|
|
|
|
if sender_domain != origin:
|
2019-06-20 11:32:02 +02:00
|
|
|
raise SynapseError(
|
|
|
|
|
400, "The invite event was not from the server sending it"
|
|
|
|
|
)
|
2017-06-30 17:20:30 +02:00
|
|
|
|
|
|
|
|
if not self.is_mine_id(event.state_key):
|
|
|
|
|
raise SynapseError(400, "The invite event must be for this server")
|
|
|
|
|
|
2018-05-18 12:18:39 +02:00
|
|
|
# block any attempts to invite the server notices mxid
|
|
|
|
|
if event.state_key == self._server_notices_mxid:
|
2020-06-16 14:51:47 +02:00
|
|
|
raise SynapseError(HTTPStatus.FORBIDDEN, "Cannot invite this user")
|
2018-05-18 12:18:39 +02:00
|
|
|
|
2021-01-29 17:38:29 +01:00
|
|
|
# We retrieve the room member handler here as to not cause a cyclic dependency
|
|
|
|
|
member_handler = self.hs.get_room_member_handler()
|
2021-02-03 11:17:37 +01:00
|
|
|
# We don't rate limit based on room ID, as that should be done by
|
|
|
|
|
# sending server.
|
2021-03-30 13:06:09 +02:00
|
|
|
await member_handler.ratelimit_invite(None, None, event.state_key)
|
2021-01-29 17:38:29 +01:00
|
|
|
|
2020-02-26 17:58:33 +01:00
|
|
|
# keep a record of the room version, if we don't yet know it.
|
|
|
|
|
# (this may get overwritten if we later get a different room version in a
|
|
|
|
|
# join dance).
|
2020-11-13 17:24:04 +01:00
|
|
|
await self._maybe_store_room_on_outlier_membership(
|
2020-02-26 17:58:33 +01:00
|
|
|
room_id=event.room_id, room_version=room_version
|
|
|
|
|
)
|
|
|
|
|
|
2014-12-05 17:20:48 +01:00
|
|
|
event.internal_metadata.outlier = True
|
2019-01-24 18:33:19 +01:00
|
|
|
event.internal_metadata.out_of_band_membership = True
|
2014-11-07 14:41:00 +01:00
|
|
|
|
|
|
|
|
event.signatures.update(
|
|
|
|
|
compute_event_signature(
|
2020-01-31 14:47:43 +01:00
|
|
|
room_version,
|
|
|
|
|
event.get_pdu_json(),
|
|
|
|
|
self.hs.hostname,
|
2020-07-08 18:51:56 +02:00
|
|
|
self.hs.signing_key,
|
2014-11-07 14:41:00 +01:00
|
|
|
)
|
|
|
|
|
)
|
|
|
|
|
|
2021-09-22 18:58:57 +02:00
|
|
|
context = EventContext.for_outlier()
|
2021-08-26 22:41:44 +02:00
|
|
|
await self._federation_event_handler.persist_events_and_notify(
|
|
|
|
|
event.room_id, [(event, context)]
|
|
|
|
|
)
|
2014-11-07 14:41:00 +01:00
|
|
|
|
2019-07-23 15:00:55 +02:00
|
|
|
return event
|
2014-11-07 14:41:00 +01:00
|
|
|
|
2020-02-03 17:19:18 +01:00
|
|
|
async def do_remotely_reject_invite(
|
|
|
|
|
self, target_hosts: Iterable[str], room_id: str, user_id: str, content: JsonDict
|
2020-05-22 15:21:54 +02:00
|
|
|
) -> Tuple[EventBase, int]:
|
2020-02-03 17:19:18 +01:00
|
|
|
origin, event, room_version = await self._make_and_verify_event(
|
2019-12-11 14:07:25 +01:00
|
|
|
target_hosts, room_id, user_id, "leave", content=content
|
2017-04-21 02:24:17 +02:00
|
|
|
)
|
2017-06-09 14:05:05 +02:00
|
|
|
# Mark as outlier as we don't have any state for this event; we're not
|
|
|
|
|
# even in the room.
|
2017-06-09 11:08:18 +02:00
|
|
|
event.internal_metadata.outlier = True
|
2019-01-24 18:33:19 +01:00
|
|
|
event.internal_metadata.out_of_band_membership = True
|
2015-10-20 12:58:58 +02:00
|
|
|
|
2020-10-23 18:38:40 +02:00
|
|
|
# Try the host that we successfully called /make_leave/ on first for
|
2017-04-07 15:39:32 +02:00
|
|
|
# the /send_leave/ request.
|
2020-07-01 17:21:02 +02:00
|
|
|
host_list = list(target_hosts)
|
2015-10-20 12:58:58 +02:00
|
|
|
try:
|
2020-07-01 17:21:02 +02:00
|
|
|
host_list.remove(origin)
|
|
|
|
|
host_list.insert(0, origin)
|
2015-10-20 12:58:58 +02:00
|
|
|
except ValueError:
|
|
|
|
|
pass
|
|
|
|
|
|
2020-07-01 17:21:02 +02:00
|
|
|
await self.federation_client.send_leave(host_list, event)
|
2016-03-15 14:24:31 +01:00
|
|
|
|
2021-09-22 18:58:57 +02:00
|
|
|
context = EventContext.for_outlier()
|
2021-08-26 22:41:44 +02:00
|
|
|
stream_id = await self._federation_event_handler.persist_events_and_notify(
|
2020-09-14 11:16:41 +02:00
|
|
|
event.room_id, [(event, context)]
|
|
|
|
|
)
|
2016-03-15 14:24:31 +01:00
|
|
|
|
2020-05-22 15:21:54 +02:00
|
|
|
return event, stream_id
|
2015-10-20 12:58:58 +02:00
|
|
|
|
2020-02-03 17:22:30 +01:00
|
|
|
async def _make_and_verify_event(
|
|
|
|
|
self,
|
|
|
|
|
target_hosts: Iterable[str],
|
|
|
|
|
room_id: str,
|
|
|
|
|
user_id: str,
|
|
|
|
|
membership: str,
|
2021-04-08 23:38:54 +02:00
|
|
|
content: JsonDict,
|
2020-07-01 17:21:02 +02:00
|
|
|
params: Optional[Dict[str, Union[str, Iterable[str]]]] = None,
|
2020-02-03 17:22:30 +01:00
|
|
|
) -> Tuple[str, EventBase, RoomVersion]:
|
2020-01-27 15:30:57 +01:00
|
|
|
(
|
|
|
|
|
origin,
|
|
|
|
|
event,
|
|
|
|
|
room_version,
|
2020-02-03 17:22:30 +01:00
|
|
|
) = await self.federation_client.make_membership_event(
|
2019-06-20 11:32:02 +02:00
|
|
|
target_hosts, room_id, user_id, membership, content, params=params
|
2015-10-20 12:58:58 +02:00
|
|
|
)
|
|
|
|
|
|
2019-01-23 21:21:33 +01:00
|
|
|
logger.debug("Got response to make_%s: %s", membership, event)
|
2015-10-20 12:58:58 +02:00
|
|
|
|
|
|
|
|
# We should assert some things.
|
|
|
|
|
# FIXME: Do this in a nicer way
|
2019-06-20 11:32:02 +02:00
|
|
|
assert event.type == EventTypes.Member
|
|
|
|
|
assert event.user_id == user_id
|
|
|
|
|
assert event.state_key == user_id
|
|
|
|
|
assert event.room_id == room_id
|
2020-01-27 15:30:57 +01:00
|
|
|
return origin, event, room_version
|
2015-10-20 12:58:58 +02:00
|
|
|
|
2020-02-03 16:40:41 +01:00
|
|
|
async def on_make_leave_request(
|
|
|
|
|
self, origin: str, room_id: str, user_id: str
|
|
|
|
|
) -> EventBase:
|
2021-02-16 23:32:34 +01:00
|
|
|
"""We've received a /make_leave/ request, so we create a partial
|
2018-07-25 23:44:41 +02:00
|
|
|
leave event for the room and return that. We do *not* persist or
|
2015-10-20 12:58:58 +02:00
|
|
|
process it until the other server has signed it and sent it back.
|
2019-07-26 11:08:22 +02:00
|
|
|
|
|
|
|
|
Args:
|
2020-02-03 16:40:41 +01:00
|
|
|
origin: The (verified) server name of the requesting server.
|
|
|
|
|
room_id: Room to create leave event in
|
|
|
|
|
user_id: The user to create the leave for
|
2015-10-20 12:58:58 +02:00
|
|
|
"""
|
2019-07-26 11:08:22 +02:00
|
|
|
if get_domain_from_id(user_id) != origin:
|
|
|
|
|
logger.info(
|
|
|
|
|
"Got /make_leave request for user %r from different origin %s, ignoring",
|
|
|
|
|
user_id,
|
|
|
|
|
origin,
|
|
|
|
|
)
|
|
|
|
|
raise SynapseError(403, "User not from origin", Codes.FORBIDDEN)
|
|
|
|
|
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj = await self.store.get_room_version(room_id)
|
|
|
|
|
builder = self.event_builder_factory.for_room_version(
|
|
|
|
|
room_version_obj,
|
2019-01-23 21:21:33 +01:00
|
|
|
{
|
|
|
|
|
"type": EventTypes.Member,
|
|
|
|
|
"content": {"membership": Membership.LEAVE},
|
|
|
|
|
"room_id": room_id,
|
|
|
|
|
"sender": user_id,
|
|
|
|
|
"state_key": user_id,
|
2019-06-20 11:32:02 +02:00
|
|
|
},
|
2019-01-23 21:21:33 +01:00
|
|
|
)
|
2015-10-20 12:58:58 +02:00
|
|
|
|
2020-02-03 16:40:41 +01:00
|
|
|
event, context = await self.event_creation_handler.create_new_client_event(
|
2019-06-20 11:32:02 +02:00
|
|
|
builder=builder
|
2015-10-20 12:58:58 +02:00
|
|
|
)
|
|
|
|
|
|
2016-04-13 12:11:46 +02:00
|
|
|
try:
|
2016-07-15 10:29:54 +02:00
|
|
|
# The remote hasn't signed it yet, obviously. We'll do the full checks
|
|
|
|
|
# when we get the event back in `on_send_leave_request`
|
Split `event_auth.check` into two parts (#10940)
Broadly, the existing `event_auth.check` function has two parts:
* a validation section: checks that the event isn't too big, that it has the rught signatures, etc.
This bit is independent of the rest of the state in the room, and so need only be done once
for each event.
* an auth section: ensures that the event is allowed, given the rest of the state in the room.
This gets done multiple times, against various sets of room state, because it forms part of
the state res algorithm.
Currently, this is implemented with `do_sig_check` and `do_size_check` parameters, but I think
that makes everything hard to follow. Instead, we split the function in two and call each part
separately where it is needed.
2021-09-29 19:59:15 +02:00
|
|
|
await self._event_auth_handler.check_auth_rules_from_context(
|
|
|
|
|
room_version_obj, event, context
|
2019-01-25 19:31:41 +01:00
|
|
|
)
|
2016-04-13 12:11:46 +02:00
|
|
|
except AuthError as e:
|
2019-10-31 11:23:24 +01:00
|
|
|
logger.warning("Failed to create new leave %r because %s", event, e)
|
2016-04-13 12:11:46 +02:00
|
|
|
raise e
|
2015-10-20 12:58:58 +02:00
|
|
|
|
2019-07-23 15:00:55 +02:00
|
|
|
return event
|
2015-10-20 12:58:58 +02:00
|
|
|
|
2021-06-09 20:39:51 +02:00
|
|
|
async def on_make_knock_request(
|
|
|
|
|
self, origin: str, room_id: str, user_id: str
|
|
|
|
|
) -> EventBase:
|
|
|
|
|
"""We've received a make_knock request, so we create a partial
|
|
|
|
|
knock event for the room and return that. We do *not* persist or
|
|
|
|
|
process it until the other server has signed it and sent it back.
|
|
|
|
|
|
|
|
|
|
Args:
|
|
|
|
|
origin: The (verified) server name of the requesting server.
|
|
|
|
|
room_id: The room to create the knock event in.
|
|
|
|
|
user_id: The user to create the knock for.
|
|
|
|
|
|
|
|
|
|
Returns:
|
|
|
|
|
The partial knock event.
|
|
|
|
|
"""
|
|
|
|
|
if get_domain_from_id(user_id) != origin:
|
|
|
|
|
logger.info(
|
2021-06-15 13:45:14 +02:00
|
|
|
"Get /make_knock request for user %r from different origin %s, ignoring",
|
2021-06-09 20:39:51 +02:00
|
|
|
user_id,
|
|
|
|
|
origin,
|
|
|
|
|
)
|
|
|
|
|
raise SynapseError(403, "User not from origin", Codes.FORBIDDEN)
|
|
|
|
|
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj = await self.store.get_room_version(room_id)
|
2021-06-09 20:39:51 +02:00
|
|
|
|
2021-09-29 11:57:10 +02:00
|
|
|
builder = self.event_builder_factory.for_room_version(
|
|
|
|
|
room_version_obj,
|
2021-06-09 20:39:51 +02:00
|
|
|
{
|
|
|
|
|
"type": EventTypes.Member,
|
|
|
|
|
"content": {"membership": Membership.KNOCK},
|
|
|
|
|
"room_id": room_id,
|
|
|
|
|
"sender": user_id,
|
|
|
|
|
"state_key": user_id,
|
|
|
|
|
},
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
event, context = await self.event_creation_handler.create_new_client_event(
|
|
|
|
|
builder=builder
|
|
|
|
|
)
|
|
|
|
|
|
2021-07-20 12:39:46 +02:00
|
|
|
event_allowed, _ = await self.third_party_event_rules.check_event_allowed(
|
2021-06-09 20:39:51 +02:00
|
|
|
event, context
|
|
|
|
|
)
|
|
|
|
|
if not event_allowed:
|
|
|
|
|
logger.warning("Creation of knock %s forbidden by third-party rules", event)
|
|
|
|
|
raise SynapseError(
|
|
|
|
|
403, "This event is not allowed in this context", Codes.FORBIDDEN
|
|
|
|
|
)
|
|
|
|
|
|
|
|
|
|
try:
|
|
|
|
|
# The remote hasn't signed it yet, obviously. We'll do the full checks
|
|
|
|
|
# when we get the event back in `on_send_knock_request`
|
Split `event_auth.check` into two parts (#10940)
Broadly, the existing `event_auth.check` function has two parts:
* a validation section: checks that the event isn't too big, that it has the rught signatures, etc.
This bit is independent of the rest of the state in the room, and so need only be done once
for each event.
* an auth section: ensures that the event is allowed, given the rest of the state in the room.
This gets done multiple times, against various sets of room state, because it forms part of
the state res algorithm.
Currently, this is implemented with `do_sig_check` and `do_size_check` parameters, but I think
that makes everything hard to follow. Instead, we split the function in two and call each part
separately where it is needed.
2021-09-29 19:59:15 +02:00
|
|
|
await self._event_auth_handler.check_auth_rules_from_context(
|
|
|
|
|
room_version_obj, event, context
|
2021-06-09 20:39:51 +02:00
|
|
|
)
|
|
|
|
|
except AuthError as e:
|
|
|
|
|
logger.warning("Failed to create new knock %r because %s", event, e)
|
|
|
|
|
raise e
|
|
|
|
|
|
|
|
|
|
return event
|
|
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
async def get_state_ids_for_pdu(self, room_id: str, event_id: str) -> List[str]:
|
2021-02-16 23:32:34 +01:00
|
|
|
"""Returns the state at the event. i.e. not including said event."""
|
2020-08-18 22:20:49 +02:00
|
|
|
event = await self.store.get_event(event_id, check_room_id=room_id)
|
2022-03-21 12:23:32 +01:00
|
|
|
if event.internal_metadata.outlier:
|
|
|
|
|
raise NotFoundError("State not known at event %s" % (event_id,))
|
2018-08-02 12:53:52 +02:00
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
state_groups = await self.state_store.get_state_groups_ids(room_id, [event_id])
|
2016-09-02 11:49:43 +02:00
|
|
|
|
2022-03-21 12:23:32 +01:00
|
|
|
# get_state_groups_ids should return exactly one result
|
|
|
|
|
assert len(state_groups) == 1
|
2016-09-02 11:49:43 +02:00
|
|
|
|
2022-03-21 12:23:32 +01:00
|
|
|
state_map = next(iter(state_groups.values()))
|
2016-09-02 11:49:43 +02:00
|
|
|
|
2022-03-21 12:23:32 +01:00
|
|
|
state_key = event.get_state_key()
|
|
|
|
|
if state_key is not None:
|
|
|
|
|
# the event was not rejected (get_event raises a NotFoundError for rejected
|
|
|
|
|
# events) so the state at the event should include the event itself.
|
|
|
|
|
assert (
|
|
|
|
|
state_map.get((event.type, state_key)) == event.event_id
|
|
|
|
|
), "State at event did not include event itself"
|
|
|
|
|
|
|
|
|
|
# ... but we need the state *before* that event
|
|
|
|
|
if "replaces_state" in event.unsigned:
|
|
|
|
|
prev_id = event.unsigned["replaces_state"]
|
|
|
|
|
state_map[(event.type, state_key)] = prev_id
|
|
|
|
|
else:
|
|
|
|
|
del state_map[(event.type, state_key)]
|
|
|
|
|
|
|
|
|
|
return list(state_map.values())
|
2016-09-02 11:49:43 +02:00
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
async def on_backfill_request(
|
|
|
|
|
self, origin: str, room_id: str, pdu_list: List[str], limit: int
|
|
|
|
|
) -> List[EventBase]:
|
2021-07-01 20:25:37 +02:00
|
|
|
in_room = await self._event_auth_handler.check_host_in_room(room_id, origin)
|
2014-11-10 12:59:51 +01:00
|
|
|
if not in_room:
|
|
|
|
|
raise AuthError(403, "Host not in room.")
|
2014-10-31 10:59:02 +01:00
|
|
|
|
2020-02-06 19:25:24 +01:00
|
|
|
# Synapse asks for 100 events per backfill request. Do not allow more.
|
|
|
|
|
limit = min(limit, 100)
|
|
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
events = await self.store.get_backfill_events(room_id, pdu_list, limit)
|

Fix historical messages backfilling in random order on remote homeservers (MSC2716) (#11114)
Fix https://github.com/matrix-org/synapse/issues/11091
Fix https://github.com/matrix-org/synapse/issues/10764 (side-stepping the issue because we no longer have to deal with `fake_prev_event_id`)
1. Made the `/backfill` response return messages in `(depth, stream_ordering)` order (previously only sorted by `depth`)
- Technically, it shouldn't really matter how `/backfill` returns things but I'm just trying to make the `stream_ordering` a little more consistent from the origin to the remote homeservers in order to get the order of messages from `/messages` consistent ([sorted by `(topological_ordering, stream_ordering)`](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)).
- Even now that we return backfilled messages in order, it still doesn't guarantee the same `stream_ordering` (and more importantly the [`/messages` order](https://github.com/matrix-org/synapse/blob/develop/docs/development/room-dag-concepts.md#depth-and-stream-ordering)) on the other server. For example, if a room has a bunch of history imported and someone visits a permalink to a historical message back in time, their homeserver will skip over the historical messages in between and insert the permalink as the next message in the `stream_order` and totally throw off the sort.
- This will be even more the case when we add the [MSC3030 jump to date API endpoint](https://github.com/matrix-org/matrix-doc/pull/3030) so the static archives can navigate and jump to a certain date.
- We're solving this in the future by switching to [online topological ordering](https://github.com/matrix-org/gomatrixserverlib/issues/187) and [chunking](https://github.com/matrix-org/synapse/issues/3785) which by its nature will apply retroactively to fix any inconsistencies introduced by people permalinking
2. As we're navigating `prev_events` to return in `/backfill`, we order by `depth` first (newest -> oldest) and now also tie-break based on the `stream_ordering` (newest -> oldest). This is technically important because MSC2716 inserts a bunch of historical messages at the same `depth` so it's best to be prescriptive about which ones we should process first. In reality, I think the code already looped over the historical messages as expected because the database is already in order.
3. Making the historical state chain and historical event chain float on their own by having no `prev_events` instead of a fake `prev_event` which caused backfill to get clogged with an unresolvable event. Fixes https://github.com/matrix-org/synapse/issues/11091 and https://github.com/matrix-org/synapse/issues/10764
4. We no longer find connected insertion events by finding a potential `prev_event` connection to the current event we're iterating over. We now solely rely on marker events which when processed, add the insertion event as an extremity and the federating homeserver can ask about it when time calls.
- Related discussion, https://github.com/matrix-org/synapse/pull/11114#discussion_r741514793
Before | After
--- | ---
 | 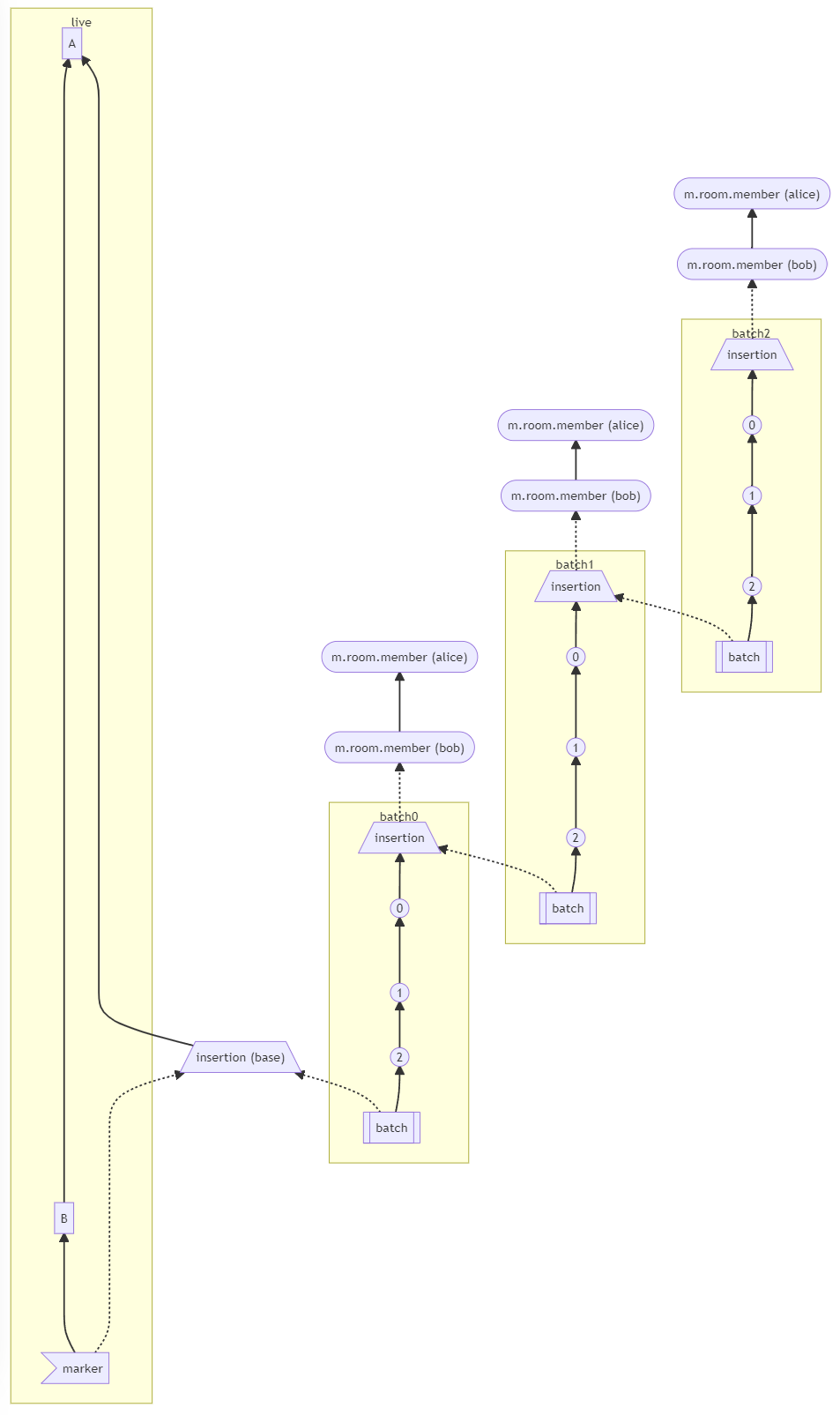
#### Why aren't we sorting topologically when receiving backfill events?
> The main reason we're going to opt to not sort topologically when receiving backfill events is because it's probably best to do whatever is easiest to make it just work. People will probably have opinions once they look at [MSC2716](https://github.com/matrix-org/matrix-doc/pull/2716) which could change whatever implementation anyway.
>
> As mentioned, ideally we would do this but code necessary to make the fake edges but it gets confusing and gives an impression of “just whyyyy” (feels icky). This problem also dissolves with online topological ordering.
>
> -- https://github.com/matrix-org/synapse/pull/11114#discussion_r741517138
See https://github.com/matrix-org/synapse/pull/11114#discussion_r739610091 for the technical difficulties
2022-02-07 22:54:13 +01:00
|
|
|
logger.debug(
|
|
|
|
|
"on_backfill_request: backfill events=%s",
|
|
|
|
|
[
|
|
|
|
|
"event_id=%s,depth=%d,body=%s,prevs=%s\n"
|
|
|
|
|
% (
|
|
|
|
|
event.event_id,
|
|
|
|
|
event.depth,
|
|
|
|
|
event.content.get("body", event.type),
|
|
|
|
|
event.prev_event_ids(),
|
|
|
|
|
)
|
|
|
|
|
for event in events
|
|
|
|
|
],
|
|
|
|
|
)
|
2014-10-31 10:59:02 +01:00
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
events = await filter_events_for_server(self.storage, origin, events)
|
2015-07-03 18:52:57 +02:00
|
|
|
|
2019-07-23 15:00:55 +02:00
|
|
|
return events
|
2014-10-31 10:59:02 +01:00
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
async def get_persisted_pdu(
|
|
|
|
|
self, origin: str, event_id: str
|
|
|
|
|
) -> Optional[EventBase]:
|
2018-06-07 17:18:57 +02:00
|
|
|
"""Get an event from the database for the given server.
|
|
|
|
|
|
|
|
|
|
Args:
|
2020-04-24 20:36:38 +02:00
|
|
|
origin: hostname of server which is requesting the event; we
|
2018-06-07 17:18:57 +02:00
|
|
|
will check that the server is allowed to see it.
|
2020-04-24 20:36:38 +02:00
|
|
|
event_id: id of the event being requested
|
2014-10-31 11:47:34 +01:00
|
|
|
|
|
|
|
|
Returns:
|
2020-04-24 20:36:38 +02:00
|
|
|
None if we know nothing about the event; otherwise the (possibly-redacted) event.
|
2018-06-07 17:18:57 +02:00
|
|
|
|
|
|
|
|
Raises:
|
|
|
|
|
AuthError if the server is not currently in the room
|
2014-10-31 11:47:34 +01:00
|
|
|
"""
|
2020-04-24 20:36:38 +02:00
|
|
|
event = await self.store.get_event(
|
2019-06-20 11:32:02 +02:00
|
|
|
event_id, allow_none=True, allow_rejected=True
|
2014-10-31 11:47:34 +01:00
|
|
|
)
|
|
|
|
|
|
|
|
|
|
if event:
|
2021-07-01 20:25:37 +02:00
|
|
|
in_room = await self._event_auth_handler.check_host_in_room(
|
|
|
|
|
event.room_id, origin
|
|
|
|
|
)
|
2018-06-07 17:18:57 +02:00
|
|
|
if not in_room:
|
|
|
|
|
raise AuthError(403, "Host not in room.")
|
2016-08-10 14:22:20 +02:00
|
|
|
|
2020-04-24 20:36:38 +02:00
|
|
|
events = await filter_events_for_server(self.storage, origin, [event])
|
2018-06-07 17:18:57 +02:00
|
|
|
event = events[0]
|
2019-07-23 15:00:55 +02:00
|
|
|
return event
|
2014-10-31 11:47:34 +01:00
|
|
|
else:
|
2019-07-23 15:00:55 +02:00
|
|
|
return None
|
2014-10-31 11:47:34 +01:00
|
|
|
|
2020-02-03 20:15:08 +01:00
|
|
|
async def on_get_missing_events(
|
2021-04-06 13:21:57 +02:00
|
|
|
self,
|
|
|
|
|
origin: str,
|
|
|
|
|
room_id: str,
|
|
|
|
|
earliest_events: List[str],
|
|
|
|
|
latest_events: List[str],
|
|
|
|
|
limit: int,
|
|
|
|
|
) -> List[EventBase]:
|
2021-07-01 20:25:37 +02:00
|
|
|
in_room = await self._event_auth_handler.check_host_in_room(room_id, origin)
|
2015-02-23 14:58:02 +01:00
|
|
|
if not in_room:
|
|
|
|
|
raise AuthError(403, "Host not in room.")
|
|
|
|
|
|
2020-02-06 19:25:24 +01:00
|
|
|
# Only allow up to 20 events to be retrieved per request.
|
2015-02-23 14:58:02 +01:00
|
|
|
limit = min(limit, 20)
|
|
|
|
|
|
2020-02-03 20:15:08 +01:00
|
|
|
missing_events = await self.store.get_missing_events(
|
2015-02-23 14:58:02 +01:00
|
|
|
room_id=room_id,
|
|
|
|
|
earliest_events=earliest_events,
|
|
|
|
|
latest_events=latest_events,
|
|
|
|
|
limit=limit,
|
|
|
|
|
)
|
|
|
|
|
|
2020-02-03 20:15:08 +01:00
|
|
|
missing_events = await filter_events_for_server(
|
2019-10-23 18:25:54 +02:00
|
|
|
self.storage, origin, missing_events
|
2018-06-08 12:34:46 +02:00
|
|
|
)
|
|
|
|
|
|
2019-07-23 15:00:55 +02:00
|
|
|
return missing_events
|
2015-02-23 14:58:02 +01:00
|
|
|
|
2020-05-01 16:15:36 +02:00
|
|
|
async def exchange_third_party_invite(
|
2021-04-06 13:21:57 +02:00
|
|
|
self, sender_user_id: str, target_user_id: str, room_id: str, signed: JsonDict
|
|
|
|
|
) -> None:
|
2019-06-20 11:32:02 +02:00
|
|
|
third_party_invite = {"signed": signed}
|
2015-12-17 18:09:51 +01:00
|
|
|
|
2015-11-05 17:43:19 +01:00
|
|
|
event_dict = {
|
|
|
|
|
"type": EventTypes.Member,
|
|
|
|
|
"content": {
|
|
|
|
|
"membership": Membership.INVITE,
|
2015-12-17 18:09:51 +01:00
|
|
|
"third_party_invite": third_party_invite,
|
2015-11-05 17:43:19 +01:00
|
|
|
},
|
|
|
|
|
"room_id": room_id,
|
2016-02-23 16:11:25 +01:00
|
|
|
"sender": sender_user_id,
|
|
|
|
|
"state_key": target_user_id,
|
2015-11-05 17:43:19 +01:00
|
|
|
}
|
|
|
|
|
|
2021-07-01 20:25:37 +02:00
|
|
|
if await self._event_auth_handler.check_host_in_room(room_id, self.hs.hostname):
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj = await self.store.get_room_version(room_id)
|
|
|
|
|
builder = self.event_builder_factory.for_room_version(
|
|
|
|
|
room_version_obj, event_dict
|
|
|
|
|
)
|
2019-01-23 21:21:33 +01:00
|
|
|
|
2019-01-28 18:00:14 +01:00
|
|
|
EventValidator().validate_builder(builder)
|
2020-05-01 16:15:36 +02:00
|
|
|
event, context = await self.event_creation_handler.create_new_client_event(
|
2016-05-11 10:09:20 +02:00
|
|
|
builder=builder
|
|
|
|
|
)
|
2015-12-17 18:31:20 +01:00
|
|
|
|
2020-05-01 16:15:36 +02:00
|
|
|
event, context = await self.add_display_name_to_third_party_invite(
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj, event_dict, event, context
|
2015-12-17 18:31:20 +01:00
|
|
|
)
|
|
|
|
|
|
2019-11-04 18:09:22 +01:00
|
|
|
EventValidator().validate_new(event, self.config)
|
2019-01-28 18:00:14 +01:00
|
|
|
|
2019-01-29 17:15:16 +01:00
|
|
|
# We need to tell the transaction queue to send this out, even
|
|
|
|
|
# though the sender isn't a local user.
|
|
|
|
|
event.internal_metadata.send_on_behalf_of = self.hs.hostname
|
|
|
|
|
|
2016-04-13 12:11:46 +02:00
|
|
|
try:
|
Split `event_auth.check` into two parts (#10940)
Broadly, the existing `event_auth.check` function has two parts:
* a validation section: checks that the event isn't too big, that it has the rught signatures, etc.
This bit is independent of the rest of the state in the room, and so need only be done once
for each event.
* an auth section: ensures that the event is allowed, given the rest of the state in the room.
This gets done multiple times, against various sets of room state, because it forms part of
the state res algorithm.
Currently, this is implemented with `do_sig_check` and `do_size_check` parameters, but I think
that makes everything hard to follow. Instead, we split the function in two and call each part
separately where it is needed.
2021-09-29 19:59:15 +02:00
|
|
|
validate_event_for_room_version(room_version_obj, event)
|
|
|
|
|
await self._event_auth_handler.check_auth_rules_from_context(
|
|
|
|
|
room_version_obj, event, context
|
2021-07-01 20:25:37 +02:00
|
|
|
)
|
2016-04-13 12:11:46 +02:00
|
|
|
except AuthError as e:
|
2019-10-31 11:23:24 +01:00
|
|
|
logger.warning("Denying new third party invite %r because %s", event, e)
|
2016-04-13 12:11:46 +02:00
|
|
|
raise e
|
|
|
|
|
|
2020-05-01 16:15:36 +02:00
|
|
|
await self._check_signature(event, context)
|
2019-11-01 11:28:09 +01:00
|
|
|
|
|
|
|
|
# We retrieve the room member handler here as to not cause a cyclic dependency
|
2018-03-01 11:54:37 +01:00
|
|
|
member_handler = self.hs.get_room_member_handler()
|
2020-05-01 16:15:36 +02:00
|
|
|
await member_handler.send_membership_event(None, event, context)
|
2015-11-05 17:43:19 +01:00
|
|
|
else:
|
2020-02-21 13:15:07 +01:00
|
|
|
destinations = {x.split(":", 1)[-1] for x in (sender_user_id, room_id)}
|
2021-07-15 11:35:46 +02:00
|
|
|
|
|
|
|
|
try:
|
|
|
|
|
await self.federation_client.forward_third_party_invite(
|
|
|
|
|
destinations, room_id, event_dict
|
|
|
|
|
)
|
|
|
|
|
except (RequestSendFailed, HttpResponseException):
|
|
|
|
|
raise SynapseError(502, "Failed to forward third party invite")
|
2015-11-05 17:43:19 +01:00
|
|
|
|
2020-02-03 17:02:50 +01:00
|
|
|
async def on_exchange_third_party_invite_request(
|
2020-11-19 11:05:33 +01:00
|
|
|
self, event_dict: JsonDict
|
2020-02-03 17:02:50 +01:00
|
|
|
) -> None:
|
2017-09-19 13:18:01 +02:00
|
|
|
"""Handle an exchange_third_party_invite request from a remote server
|
|
|
|
|
|
|
|
|
|
The remote server will call this when it wants to turn a 3pid invite
|
|
|
|
|
into a normal m.room.member invite.
|
|
|
|
|
|
2019-09-11 11:37:17 +02:00
|
|
|
Args:
|
2020-11-19 11:05:33 +01:00
|
|
|
event_dict: Dictionary containing the event body.
|
2019-09-11 11:37:17 +02:00
|
|
|
|
2017-09-19 13:18:01 +02:00
|
|
|
"""
|
2020-11-19 11:05:33 +01:00
|
|
|
assert_params_in_dict(event_dict, ["room_id"])
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj = await self.store.get_room_version(event_dict["room_id"])
|
2019-01-23 21:21:33 +01:00
|
|
|
|
|
|
|
|
# NB: event_dict has a particular specced format we might need to fudge
|
|
|
|
|
# if we change event formats too much.
|
2021-09-29 11:57:10 +02:00
|
|
|
builder = self.event_builder_factory.for_room_version(
|
|
|
|
|
room_version_obj, event_dict
|
|
|
|
|
)
|
2015-11-05 17:43:19 +01:00
|
|
|
|
2020-02-03 17:02:50 +01:00
|
|
|
event, context = await self.event_creation_handler.create_new_client_event(
|
2019-06-20 11:32:02 +02:00
|
|
|
builder=builder
|
2015-11-05 17:43:19 +01:00
|
|
|
)
|
2020-02-03 17:02:50 +01:00
|
|
|
event, context = await self.add_display_name_to_third_party_invite(
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj, event_dict, event, context
|
2015-12-17 18:31:20 +01:00
|
|
|
)
|
|
|
|
|
|
2016-04-13 12:11:46 +02:00
|
|
|
try:
|
Split `event_auth.check` into two parts (#10940)
Broadly, the existing `event_auth.check` function has two parts:
* a validation section: checks that the event isn't too big, that it has the rught signatures, etc.
This bit is independent of the rest of the state in the room, and so need only be done once
for each event.
* an auth section: ensures that the event is allowed, given the rest of the state in the room.
This gets done multiple times, against various sets of room state, because it forms part of
the state res algorithm.
Currently, this is implemented with `do_sig_check` and `do_size_check` parameters, but I think
that makes everything hard to follow. Instead, we split the function in two and call each part
separately where it is needed.
2021-09-29 19:59:15 +02:00
|
|
|
validate_event_for_room_version(room_version_obj, event)
|
|
|
|
|
await self._event_auth_handler.check_auth_rules_from_context(
|
|
|
|
|
room_version_obj, event, context
|
2021-07-01 20:25:37 +02:00
|
|
|
)
|
2016-04-13 12:11:46 +02:00
|
|
|
except AuthError as e:
|
2019-10-31 11:23:24 +01:00
|
|
|
logger.warning("Denying third party invite %r because %s", event, e)
|
2016-04-13 12:11:46 +02:00
|
|
|
raise e
|
2020-02-03 17:02:50 +01:00
|
|
|
await self._check_signature(event, context)
|
2015-11-05 17:43:19 +01:00
|
|
|
|
2019-01-29 17:15:16 +01:00
|
|
|
# We need to tell the transaction queue to send this out, even
|
|
|
|
|
# though the sender isn't a local user.
|
|
|
|
|
event.internal_metadata.send_on_behalf_of = get_domain_from_id(event.sender)
|
|
|
|
|
|
2019-11-01 11:28:09 +01:00
|
|
|
# We retrieve the room member handler here as to not cause a cyclic dependency
|
2018-03-01 11:54:37 +01:00
|
|
|
member_handler = self.hs.get_room_member_handler()
|
2020-02-03 17:02:50 +01:00
|
|
|
await member_handler.send_membership_event(None, event, context)
|
2015-11-05 17:43:19 +01:00
|
|
|
|
2020-05-11 21:12:46 +02:00
|
|
|
async def add_display_name_to_third_party_invite(
|
2021-04-06 13:21:57 +02:00
|
|
|
self,
|
2021-09-29 11:57:10 +02:00
|
|
|
room_version_obj: RoomVersion,
|
2021-04-06 13:21:57 +02:00
|
|
|
event_dict: JsonDict,
|
|
|
|
|
event: EventBase,
|
|
|
|
|
context: EventContext,
|
|
|
|
|
) -> Tuple[EventBase, EventContext]:
|
2015-12-17 18:31:20 +01:00
|
|
|
key = (
|
|
|
|
|
EventTypes.ThirdPartyInvite,
|
2019-06-20 11:32:02 +02:00
|
|
|
event.content["third_party_invite"]["signed"]["token"],
|
2015-12-17 18:31:20 +01:00
|
|
|
)
|
2016-08-25 18:32:22 +02:00
|
|
|
original_invite = None
|
2020-05-11 21:12:46 +02:00
|
|
|
prev_state_ids = await context.get_prev_state_ids()
|
2018-07-23 14:00:22 +02:00
|
|
|
original_invite_id = prev_state_ids.get(key)
|
2016-08-25 18:32:22 +02:00
|
|
|
if original_invite_id:
|
2020-05-11 21:12:46 +02:00
|
|
|
original_invite = await self.store.get_event(
|
2016-08-25 18:32:22 +02:00
|
|
|
original_invite_id, allow_none=True
|
|
|
|
|
)
|
2016-09-22 11:56:53 +02:00
|
|
|
if original_invite:
|
2019-10-02 12:16:38 +02:00
|
|
|
# If the m.room.third_party_invite event's content is empty, it means the
|
2019-10-04 12:16:19 +02:00
|
|
|
# invite has been revoked. In this case, we don't have to raise an error here
|
|
|
|
|
# because the auth check will fail on the invite (because it's not able to
|
|
|
|
|
# fetch public keys from the m.room.third_party_invite event's content, which
|
2019-10-04 12:21:24 +02:00
|
|
|
# is empty).
|
2019-10-04 12:16:19 +02:00
|
|
|
display_name = original_invite.content.get("display_name")
|
2019-10-04 12:18:28 +02:00
|
|
|
event_dict["content"]["third_party_invite"]["display_name"] = display_name
|
2016-09-22 11:56:53 +02:00
|
|
|
else:
|
2015-12-17 18:31:20 +01:00
|
|
|
logger.info(
|
2019-06-20 11:32:02 +02:00
|
|
|
"Could not find invite event for third_party_invite: %r", event_dict
|
2015-12-17 18:31:20 +01:00
|
|
|
)
|
2016-09-22 12:59:46 +02:00
|
|
|
# We don't discard here as this is not the appropriate place to do
|
|
|
|
|
# auth checks. If we need the invite and don't have it then the
|
|
|
|
|
# auth check code will explode appropriately.
|
2015-12-17 18:31:20 +01:00
|
|
|
|
2021-09-29 11:57:10 +02:00
|
|
|
builder = self.event_builder_factory.for_room_version(
|
|
|
|
|
room_version_obj, event_dict
|
|
|
|
|
)
|
2019-01-28 18:00:14 +01:00
|
|
|
EventValidator().validate_builder(builder)
|
2020-05-11 21:12:46 +02:00
|
|
|
event, context = await self.event_creation_handler.create_new_client_event(
|
2019-06-20 11:32:02 +02:00
|
|
|
builder=builder
|
2018-01-15 17:52:07 +01:00
|
|
|
)
|
2019-11-19 15:07:39 +01:00
|
|
|
EventValidator().validate_new(event, self.config)
|
2021-09-23 12:59:07 +02:00
|
|
|
return event, context
|
2015-12-17 18:31:20 +01:00
|
|
|
|
2021-04-06 13:21:57 +02:00
|
|
|
async def _check_signature(self, event: EventBase, context: EventContext) -> None:
|
2016-02-23 16:11:25 +01:00
|
|
|
"""
|
|
|
|
|
Checks that the signature in the event is consistent with its invite.
|
|
|
|
|
|
2016-04-01 17:08:59 +02:00
|
|
|
Args:
|
2021-04-06 13:21:57 +02:00
|
|
|
event: The m.room.member event to check
|
|
|
|
|
context:
|
2016-04-01 17:08:59 +02:00
|
|
|
|
|
|
|
|
Raises:
|
|
|
|
|
AuthError: if signature didn't match any keys, or key has been
|
2016-02-23 16:11:25 +01:00
|
|
|
revoked,
|
2016-04-01 17:08:59 +02:00
|
|
|
SynapseError: if a transient error meant a key couldn't be checked
|
2016-02-23 16:11:25 +01:00
|
|
|
for revocation.
|
|
|
|
|
"""
|
|
|
|
|
signed = event.content["third_party_invite"]["signed"]
|
|
|
|
|
token = signed["token"]
|
2015-11-05 17:43:19 +01:00
|
|
|
|
2020-05-11 21:12:46 +02:00
|
|
|
prev_state_ids = await context.get_prev_state_ids()
|
2019-06-20 11:32:02 +02:00
|
|
|
invite_event_id = prev_state_ids.get((EventTypes.ThirdPartyInvite, token))
|
2015-11-05 17:43:19 +01:00
|
|
|
|
2016-08-25 18:32:22 +02:00
|
|
|
invite_event = None
|
|
|
|
|
if invite_event_id:
|
2020-05-11 21:12:46 +02:00
|
|
|
invite_event = await self.store.get_event(invite_event_id, allow_none=True)
|
2016-08-25 18:32:22 +02:00
|
|
|
|
2016-02-23 16:11:25 +01:00
|
|
|
if not invite_event:
|
|
|
|
|
raise AuthError(403, "Could not find invite")
|
|
|
|
|
|
2019-06-18 23:51:24 +02:00
|
|
|
logger.debug("Checking auth on event %r", event.content)
|
|
|
|
|
|
2021-07-16 19:22:36 +02:00
|
|
|
last_exception: Optional[Exception] = None
|
2020-07-01 17:21:02 +02:00
|
|
|
|
2019-06-18 23:51:24 +02:00
|
|
|
# for each public key in the 3pid invite event
|
2021-07-01 20:25:37 +02:00
|
|
|
for public_key_object in event_auth.get_public_keys(invite_event):
|
2016-02-23 16:11:25 +01:00
|
|
|
try:
|
2019-06-18 23:51:24 +02:00
|
|
|
# for each sig on the third_party_invite block of the actual invite
|
2016-02-23 16:11:25 +01:00
|
|
|
for server, signature_block in signed["signatures"].items():
|
2021-04-20 12:50:49 +02:00
|
|
|
for key_name in signature_block.keys():
|
2016-02-23 16:11:25 +01:00
|
|
|
if not key_name.startswith("ed25519:"):
|
|
|
|
|
continue
|
|
|
|
|
|
2019-06-18 23:51:24 +02:00
|
|
|
logger.debug(
|
|
|
|
|
"Attempting to verify sig with key %s from %r "
|
|
|
|
|
"against pubkey %r",
|
2019-06-20 11:32:02 +02:00
|
|
|
key_name,
|
|
|
|
|
server,
|
|
|
|
|
public_key_object,
|
2016-02-23 16:11:25 +01:00
|
|
|
)
|
2019-06-18 23:51:24 +02:00
|
|
|
|
|
|
|
|
try:
|
|
|
|
|
public_key = public_key_object["public_key"]
|
|
|
|
|
verify_key = decode_verify_key_bytes(
|
2019-06-20 11:32:02 +02:00
|
|
|
key_name, decode_base64(public_key)
|
2019-06-18 23:51:24 +02:00
|
|
|
)
|
|
|
|
|
verify_signed_json(signed, server, verify_key)
|
|
|
|
|
logger.debug(
|
|
|
|
|
"Successfully verified sig with key %s from %r "
|
|
|
|
|
"against pubkey %r",
|
2019-06-20 11:32:02 +02:00
|
|
|
key_name,
|
|
|
|
|
server,
|
|
|
|
|
public_key_object,
|
2019-06-18 23:51:24 +02:00
|
|
|
)
|
|
|
|
|
except Exception:
|
|
|
|
|
logger.info(
|
|
|
|
|
"Failed to verify sig with key %s from %r "
|
|
|
|
|
"against pubkey %r",
|
2019-06-20 11:32:02 +02:00
|
|
|
key_name,
|
|
|
|
|
server,
|
|
|
|
|
public_key_object,
|
2019-06-18 23:51:24 +02:00
|
|
|
)
|
|
|
|
|
raise
|
|
|
|
|
try:
|
|
|
|
|
if "key_validity_url" in public_key_object:
|
2020-05-11 21:12:46 +02:00
|
|
|
await self._check_key_revocation(
|
2019-06-20 11:32:02 +02:00
|
|
|
public_key, public_key_object["key_validity_url"]
|
2019-06-18 23:51:24 +02:00
|
|
|
)
|
|
|
|
|
except Exception:
|
|
|
|
|
logger.info(
|
|
|
|
|
"Failed to query key_validity_url %s",
|
2019-06-20 11:32:02 +02:00
|
|
|
public_key_object["key_validity_url"],
|
2016-02-23 16:11:25 +01:00
|
|
|
)
|
2019-06-18 23:51:24 +02:00
|
|
|
raise
|
2016-02-23 16:11:25 +01:00
|
|
|
return
|
|
|
|
|
except Exception as e:
|
|
|
|
|
last_exception = e
|
2020-07-01 17:21:02 +02:00
|
|
|
|
|
|
|
|
if last_exception is None:
|
|
|
|
|
# we can only get here if get_public_keys() returned an empty list
|
|
|
|
|
# TODO: make this better
|
|
|
|
|
raise RuntimeError("no public key in invite event")
|
|
|
|
|
|
2016-02-23 16:11:25 +01:00
|
|
|
raise last_exception
|
|
|
|
|
|
2021-04-06 13:21:57 +02:00
|
|
|
async def _check_key_revocation(self, public_key: str, url: str) -> None:
|
2016-02-23 16:11:25 +01:00
|
|
|
"""
|
|
|
|
|
Checks whether public_key has been revoked.
|
|
|
|
|
|
2016-04-01 17:08:59 +02:00
|
|
|
Args:
|
2021-04-06 13:21:57 +02:00
|
|
|
public_key: base-64 encoded public key.
|
|
|
|
|
url: Key revocation URL.
|
2016-02-23 16:11:25 +01:00
|
|
|
|
2016-04-01 17:08:59 +02:00
|
|
|
Raises:
|
|
|
|
|
AuthError: if they key has been revoked.
|
|
|
|
|
SynapseError: if a transient error meant a key couldn't be checked
|
2016-02-23 16:11:25 +01:00
|
|
|
for revocation.
|
|
|
|
|
"""
|
2015-11-05 17:43:19 +01:00
|
|
|
try:
|
2020-05-11 21:12:46 +02:00
|
|
|
response = await self.http_client.get_json(url, {"public_key": public_key})
|
2015-11-05 17:43:19 +01:00
|
|
|
except Exception:
|
2019-06-20 11:32:02 +02:00
|
|
|
raise SynapseError(502, "Third party certificate could not be checked")
|
2015-11-05 17:43:19 +01:00
|
|
|
if "valid" not in response or not response["valid"]:
|
|
|
|
|
raise AuthError(403, "Third party certificate was invalid")
|
2018-07-25 17:00:38 +02:00
|
|
|
|
2020-02-03 17:27:05 +01:00
|
|
|
async def _clean_room_for_join(self, room_id: str) -> None:
|
2018-08-09 11:29:48 +02:00
|
|
|
"""Called to clean up any data in DB for a given room, ready for the
|
|
|
|
|
server to join the room.
|
|
|
|
|
|
|
|
|
|
Args:
|
2020-02-03 17:27:05 +01:00
|
|
|
room_id
|
2018-08-09 11:29:48 +02:00
|
|
|
"""
|
2021-09-13 19:07:12 +02:00
|
|
|
if self.config.worker.worker_app:
|
2020-02-03 17:27:05 +01:00
|
|
|
await self._clean_room_for_join_client(room_id)
|
2018-08-09 11:29:48 +02:00
|
|
|
else:
|
2020-02-03 17:27:05 +01:00
|
|
|
await self.store.clean_room_for_join(room_id)
|
2018-07-25 17:00:38 +02:00
|
|
|
|
2020-07-24 16:53:25 +02:00
|
|
|
async def get_room_complexity(
|
|
|
|
|
self, remote_room_hosts: List[str], room_id: str
|
|
|
|
|
) -> Optional[dict]:
|
2019-07-29 18:47:27 +02:00
|
|
|
"""
|
|
|
|
|
Fetch the complexity of a remote room over federation.
|
|
|
|
|
|
|
|
|
|
Args:
|
|
|
|
|
remote_room_hosts (list[str]): The remote servers to ask.
|
|
|
|
|
room_id (str): The room ID to ask about.
|
|
|
|
|
|
|
|
|
|
Returns:
|
2020-07-24 16:53:25 +02:00
|
|
|
Dict contains the complexity
|
2019-07-29 18:47:27 +02:00
|
|
|
metric versions, while None means we could not fetch the complexity.
|
|
|
|
|
"""
|
|
|
|
|
|
|
|
|
|
for host in remote_room_hosts:
|
2020-05-11 21:12:46 +02:00
|
|
|
res = await self.federation_client.get_room_complexity(host, room_id)
|
2019-07-29 18:47:27 +02:00
|
|
|
|
|
|
|
|
# We got a result, return it.
|
|
|
|
|
if res:
|
2020-05-11 21:12:46 +02:00
|
|
|
return res
|
2019-07-29 18:47:27 +02:00
|
|
|
|
|
|
|
|
# We fell off the bottom, couldn't get the complexity from anyone. Oh
|
|
|
|
|
# well.
|
2020-05-11 21:12:46 +02:00
|
|
|
return None
|
2022-04-12 15:23:43 +02:00
|
|
|
|
|
|
|
|
async def _sync_partial_state_room(
|
|
|
|
|
self,
|
|
|
|
|
destination: str,
|
|
|
|
|
room_id: str,
|
|
|
|
|
) -> None:
|
|
|
|
|
"""Background process to resync the state of a partial-state room
|
|
|
|
|
|
|
|
|
|
Args:
|
|
|
|
|
destination: homeserver to pull the state from
|
|
|
|
|
room_id: room to be resynced
|
|
|
|
|
"""
|
|
|
|
|
|
|
|
|
|
# TODO(faster_joins): do we need to lock to avoid races? What happens if other
|
|
|
|
|
# worker processes kick off a resync in parallel? Perhaps we should just elect
|
|
|
|
|
# a single worker to do the resync.
|
|
|
|
|
#
|
|
|
|
|
# TODO(faster_joins): what happens if we leave the room during a resync? if we
|
|
|
|
|
# really leave, that might mean we have difficulty getting the room state over
|
|
|
|
|
# federation.
|
|
|
|
|
#
|
|
|
|
|
# TODO(faster_joins): try other destinations if the one we have fails
|
|
|
|
|
|
|
|
|
|
logger.info("Syncing state for room %s via %s", room_id, destination)
|
|
|
|
|
|
|
|
|
|
# we work through the queue in order of increasing stream ordering.
|
|
|
|
|
while True:
|
|
|
|
|
batch = await self.store.get_partial_state_events_batch(room_id)
|
|
|
|
|
if not batch:
|
|
|
|
|
# all the events are updated, so we can update current state and
|
|
|
|
|
# clear the lazy-loading flag.
|
|
|
|
|
logger.info("Updating current state for %s", room_id)
|
|
|
|
|
assert (
|
|
|
|
|
self.storage.persistence is not None
|
|
|
|
|
), "TODO(faster_joins): support for workers"
|
|
|
|
|
await self.storage.persistence.update_current_state(room_id)
|
|
|
|
|
|
|
|
|
|
logger.info("Clearing partial-state flag for %s", room_id)
|
|
|
|
|
success = await self.store.clear_partial_state_room(room_id)
|
|
|
|
|
if success:
|
|
|
|
|
logger.info("State resync complete for %s", room_id)
|
|
|
|
|
|
|
|
|
|
# TODO(faster_joins) update room stats and user directory?
|
|
|
|
|
return
|
|
|
|
|
|
|
|
|
|
# we raced against more events arriving with partial state. Go round
|
|
|
|
|
# the loop again. We've already logged a warning, so no need for more.
|
|
|
|
|
# TODO(faster_joins): there is still a race here, whereby incoming events which raced
|
|
|
|
|
# with us will fail to be persisted after the call to `clear_partial_state_room` due to
|
|
|
|
|
# having partial state.
|
|
|
|
|
continue
|
|
|
|
|
|
|
|
|
|
events = await self.store.get_events_as_list(
|
|
|
|
|
batch,
|
|
|
|
|
redact_behaviour=EventRedactBehaviour.AS_IS,
|
|
|
|
|
allow_rejected=True,
|
|
|
|
|
)
|
|
|
|
|
for event in events:
|
|
|
|
|
await self._federation_event_handler.update_state_for_partial_state_event(
|
|
|
|
|
destination, event
|
|
|
|
|
)
|